As international travel starts to open up for tourists, criminals are already redeploying established fraud schemes and unveiling new schemes for the post-COVID-19 landscape. One prominent scheme is the provision of fraudulent travel services by cybercriminals on both the surface web and dark web. This scheme involves using stolen payment cards or travel points to purchase various travel services and then selling the services at a discounted price to both witting and unwitting customers. Commonly purchased travel services include plane tickets, hotel bookings, rental cars, and other travel-related items.
Cybercriminals offer travel services on dark web forums, social media, or messaging apps (most commonly, Telegram), and through fraudulent travel agencies. Telegram has become a popular advertising platform for cybercriminals because it allows them to reach a wider audience and is anonymous. Unlike for dark web forums, potential customers do not need to use special software to access Telegram nor do they need to register on dark web forums. Lastly, a subset of cybercriminals have created fraudulent travel agencies that appear legitimate and offer discounted travel services to unwitting customers. This practice is most common in the former Soviet Union (FSU).
Gemini analyzed the frequency of keyword mentions across the dark web for English and Russian-language words associated with travel. As shown in the graph below, there appears to have been steady cybercriminal interest in these topics from July 2019 to March 2020. Interest in these topics spiked right before the COVID-19 travel restrictions were set in place, and then declined during the peak of the COVID-19 pandemic. At the same time, it should be noted that criminal interest in these topics rose sharply in early August 2020, which coincided with various countries opening their borders to tourism. This indicates that interest in travel fraud rises as travel restrictions are removed.
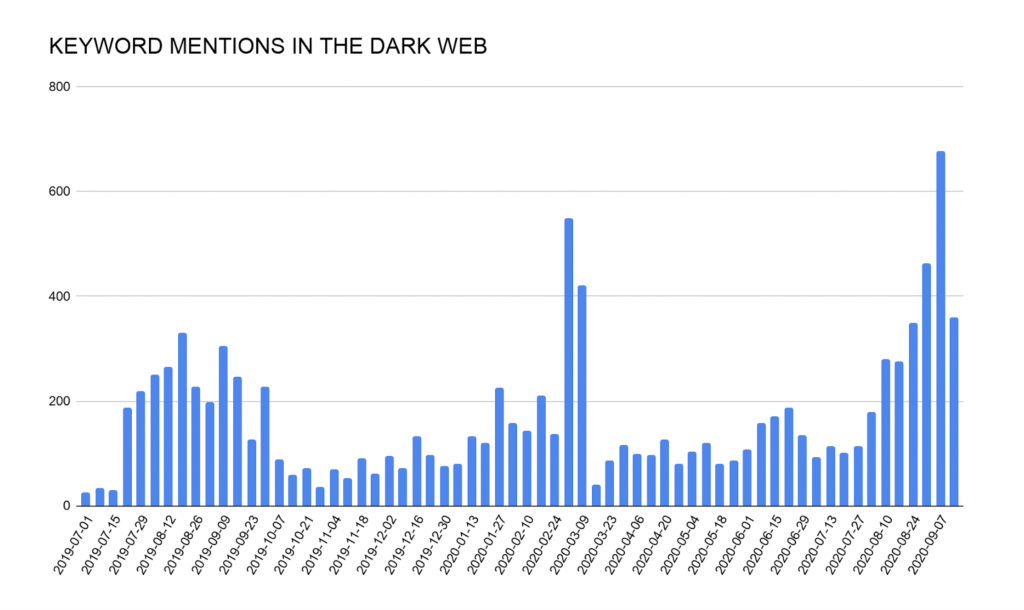 Image 1: Cybercriminal interest was steady from July 2019 to March 2020 before the COVID-19 pandemic and declined during the pandemic. Interest started to rise as the world started opening up after the pandemic.
Image 1: Cybercriminal interest was steady from July 2019 to March 2020 before the COVID-19 pandemic and declined during the pandemic. Interest started to rise as the world started opening up after the pandemic.
Additionally, since the beginning of July 2020, numerous dark web forum members and Telegram channels have resumed advertising travel services after being dormant during the peak of COVID-19 pandemic. For example, one prominent cybercriminal has posted travel advertisements daily on Telegram since the beginning of July, after making only three advertisements from March to June 28, 2020.
The premise of this fraud scheme is to make fraudulent purchases on well-known booking sites or through travel service providers, and then to direct customers to send payments to cybercriminals’ accounts. Underground forums and Telegram channels provide a platform for cybercriminals to advertise their travel services, which includes booking flights, hotels, rental cars, and other services associated with travel. Fraudsters typically offer their travel services at a significant discount, attracting not only cybercriminals but also regular travelers who are unaware of the fraud scheme.
 Image 2: How cybercriminals commit travel services fraud.
Image 2: How cybercriminals commit travel services fraud.
Cybercriminals offering travel services typically list which booking services can be used, such as booking.com, airbnb.com, and others. The customers can then choose where and when they want their bookings to be. As an example, a customer could choose a $1,000 booking at a hotel in Vietnam, send the booking to the cybercriminal, and the cybercriminal would offer to complete the booking for $500 (50% discount).
One threat actor, for example, has operated a Telegram channel since early 2020 that specializes in discount travel services. These include 70 to 80% discounts on hotels, apartments, villas, houses, and other accommodations, and 40% discounts on flights. In the advertisements, the channel points out that accommodations can be booked for one to 20 days, and zero to 21 days in advance. Furthermore, they offer refunds and guarantee that customers will be able to safely use the purchased services.
Another fraudster advertises travel services on various English- and Russian-speaking dark web forums. These include travel and wedding services with large discounts, which the actor claims are popular with famous bloggers, television stars, and show business stars. The service purportedly works through a guarantor, which adds more credibility to this fraudster, and if things go sour, their client would likely be reimbursed. To further promote the service, the actor often posts pictures on their Telegram channel of vacationing customers showing the service’s name. In general, fraudsters advertise these images to convince potential customers that the given services are actually provided.
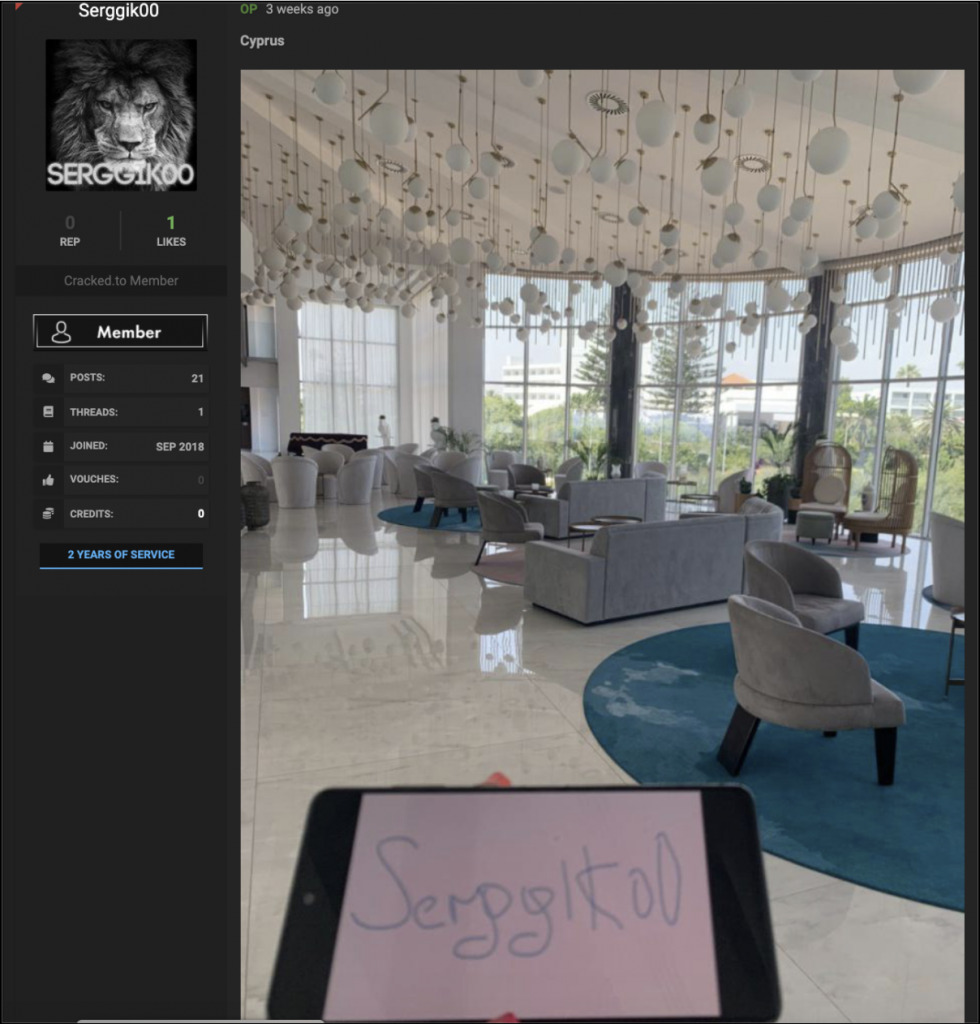 Image 3: An example of proof of travel provided by a Serggik00 customer.
Image 3: An example of proof of travel provided by a Serggik00 customer.
While booking sites employ anti-fraud systems to prevent travel services fraud, Gemini has identified a range of tactics and exploits deployed by cybercriminals to deceive anti-fraud systems. The tactics and exploits reveal how cybercriminals attempt to stay one step ahead in the game of cat-and-mouse between fraudsters and booking sites.
Anti-fraud systems detect fraudulent purchases by identifying incongruencies between payment card billing addresses, locations of purchase, and other data. To counteract these measures, cybercriminals deploy a range of technical tools to obfuscate their identities and locations. In a tutorial posted to a dark web marketplace, one threat actor explained how to imitate a victim’s identity using systems such as Sphere, which has been previously covered by Gemini. Another threat actor explained how to anonymize identities with VPNs and proxies in a tutorial posted to a dark web forum.
Criminal posts this year have included interest in purchasing emails and logs with cookies of Airbnb, HomeAway, and Rentalialogs hosts. This type of information would allow cybercriminals to impersonate account users, such as hosts, and conduct fraudulent activity, such as making fraudulent bookings. Cybercriminals believe that travel agencies devote extra attention to monitoring new accounts for fraud, which has driven up demand for active accounts with an established booking history.
Once cybercriminals have access to a compromised account, they often “warm up the account,” which involves impersonating a legitimate accountholder by imitating the searches and actions of someone looking for accommodations. Cybercriminals believe this prevents the anti-fraud system from detecting unusual activity, thereby raising the chances of success. In mid-2020, Gemini observed one actor that posted on Telegram about the sale of a script that increases the activity of Airbnb accounts. According to the post, the script had multiple functions, such as selecting dates for booking, looking at different properties in a specific price range, looking at property photos, reading full descriptions of listings, checking maps, reading reviews, and so on. A script such as this one would allow a cybercriminal to simultaneously prep multiple accounts for fraudulent activity.
Loyalty fraud, which leverages stolen loyalty points that can be used to purchase flights or hotels, presents another vector for fraud. This can include using stolen payment cards to purchase loyalty points, which can often be cashed in faster than anti-fraud systems discover that a stolen card placed the initial payment. While this is the most common type of loyalty fraud, some fraudsters use travel points from compromised loyalty accounts or social engineering techniques to gain access to corporate booking agents’ accounts. It is also more difficult to detect fraud through hotel or flight transactions purchased through loyalty points than a payment card.
Typical travel services fraud requires the cybercriminal to find a customer before monetizing the stolen payment card data or compromised accounts. To avoid this step, cybercriminals have begun actively looking to partner with so-called “dark hosts,” which are hotel owners or vacation rental hosts willing to engage in fraud. In this scheme, the cybercriminal uses stolen data to book accommodations at the partner’s lodgings and then the cybercriminal and dark host split the proceeds. As one threat actor noted in a Russian-language dark web forum, this scheme may be attractive to hotels due to the financial difficulties caused by travel restrictions.
To commit this type of fraud, a threat actor on a dark web forum recommended that attackers use compromised Airbnb accounts to make the bookings. To evade Airbnb’s anti-fraud system, the actor advised performing account warmup, as covered above. In addition, the actor noted that fraudulent bookings are more likely to succeed if the compromised account already has a linked payment card than if the attacker links a new card.

Image 4: Cybercriminals partner with hotel owners and vacation rental hosts to commit fraud.
Cybercriminals have identified several gaps in booking sites’ anti-fraud monitoring that increase the chances of success. Multiple threat actors on Telegram and dark web forums, for example, stipulate how long bookings can be made for and how much in advance they must be made. This aligns with cybercriminals’ belief that making a booking just weeks before the date reduces the likelihood that the booking will be canceled. If the booking is flagged as fraudulent and canceled, cybercriminals may instruct the customer to pay for the accommodations in cash and ensure the customer that the cybercriminal will reimburse them.
One threat actor noted in a travel fraud tutorial posted to a dark web forum that airlines will permit flight bookings if there are three or fewer spelling mistakes in the passenger’s name. Fraudsters intentionally exploit this by booking a flight under a name that has been blacklisted but spelled intentionally wrong to deceive the blacklist. Once the passenger arrives at the airport, an airport employee corrects the spelling of the name in the system, but the name is not checked against the blacklist again, enabling the passenger to board the flight.
Many companies implement multi-factor authentication (MFA) in order to avoid fraud on their sites. Cybercriminals, however, often find various ways to bypass MFA through technical means or social engineering. One post on a Russian-language dark web forum described how to use social engineering to bypass MFA on booking.com. Methods such as this often involve the attacker using accessible information, such as booking information, to trick a customer service representative into giving the attacker access to the account.
Some booking sites devote extra anti-fraud attention to, or outright prohibit, bookings purchased with foreign payment cards. As a result, cybercriminals have begun to identify sites that use these mechanisms and offer methods to overcome them. One threat actor, for example, posted to offer their services for making fraudulent bookings with stolen Japanese payment cards. They wrote that they used the booking website nta[.]co[.]jp, and noted that they have been using this site for a long time to place bookings all over the world. Additionally, they wrote that when booking through booking.com, it is better to use cards issued by Japanese banks and to set up proxies to Japan.
Due to the illegal aspect of fraudulent travel services, law enforcement seeks and prosecutes travelers using these services. According to a Computer Weekly article from October 2017, Europol, in partnership with public and private sector organizations, arrested 195 individuals that were tied to airline ticket fraud. This was a focused operation targeting travelers with fraudulently purchased tickets over a span of a few days. In November 2019, Interpol, in cooperation with other agencies, arrested another 79 individuals that were using stolen payment cards to purchase airline tickets. These specific operations are part of international law enforcement agencies’ year-round efforts to combat rising levels of fraudulent online ticket purchases, which Interpol estimates cost the airline industry close to $1 billion per year.
Though the Russian Federation seldom arrests cybercriminals within its territory, the Russian authorities do arrest cybercriminals for breaking certain unwritten rules, such as targeting Russian citizens, or for political reasons, as described in a recent Gemini article. As such, in August 2020, Russia’s Directorate “K” (the cybercrime-fighting unit of the Ministry of Interior), arrested members of the “Gods Of Logs” cybercriminal ring. One of the charges was for using stolen payment cards to make bookings on booking.com.
Aside from law enforcement arrests, there are instances in which unwitting individuals become the victims of fraudulent travel services. According to an October 2019 article in the Russian-language version of the magazine Cosmopolitan, two Russian actresses, Natalia Rudova and Nastasya Samburskaya, claimed that they were victims of fraudulent travel services. According to the actresses, many Russian bloggers and actors were advertising the travel agency traveltrips[.]ru, which purports to be a Russian-language travel booking website. The actresses claimed that the site operators offered them a large discount on their bookings in exchange for a promotional post on their social media pages. Upon checking into their hotel in Cannes, France, the actresses provided their own credit cards for room service; however, two and a half months after their vacation, their cards were charged the full amount of their hotel stay. According to the actresses, their hotel rooms and friends’ hotel rooms had been booked with stolen credit cards.
Ultimately, travel services fraud relies on customers looking for a more affordable way to travel. Therefore, tourists looking to vacation on a budget should always turn to well-known, established booking sites for one of the many deals offered at any given time. If a tourist happens across a deal that appears too good to be true on an unknown travel services site, social media, or a platform like Telegram, they should proceed with extra caution as there is a distinct possibility it could be part of a fraud scheme. The consequences for knowingly or unknowingly participating in travel fraud can very often accelerate beyond being scammed by the scammers to receiving legal repercussions from the relevant authorities.
As COVID-19 restrictions are being lifted and travel increases, cybercriminals are returning to their old methods of fraud. Travel fraud is fairly easy and profitable, making it an attractive scheme with low barriers to entry. As more individuals are starting to travel again, there is a corresponding increase in the volume and frequency of fraudulent travel offers. Gemini analysts assess with high confidence that this trend will likely continue as travel increases.
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.