
Gemini Advisory’s analysts uncovered a September 14, 2020 post on a Russian-language dark web forum by a cybercriminal group operating under the moniker “LockBit,” in which they advertised starting their own blog under the same name. LockBit is a Russian-language ransomware team, alongside “REvil”/”Sodinokibi” and “Maze,” that advertises its services on Russian-language dark web forums. Gemini has written a report, Ransomware – The New Cost of Business, that describes how ransomware teams are formed, their structure, and their operations. Additionally, the report describes the Ransomware-as-a-Service (RaaS) model, which these teams often adopt. Well-established ransomware teams use dark web forum platforms and their own blogs to intimidate victims into paying the ransom after an attack. This entry into the “big leagues” by LockBit was accompanied by a blog post with two databases from their victims: Yaskawa Electric Corporation and Overseas Express Shipping Company. The database for Yaskawa Electric Corporation contains proprietary information, such as records of purchases, bank accounts, and technical product information, as well as other internal documents. The database for Overseas Express Shipping Company contains 5.8 million records, including personally identifiable information (PII), such as names, addresses, email addresses, and other internal documents.
On August 22, 2020, on a second Russian-language dark web forum, actor “BETTER PAY” created a post addressing Yaskawa Electric Corporation and demanding a ransom payment within seven days. According to the post, if the company failed to meet this deadline, BETTER PAY would publish its data. Additionally, the post included a screenshot of what appear to be files and folders with Japanese writing, presumably from the company. Since BETTER PAY’s account was registered on the same day that it created this post, it is likely a throw-away account created specifically for this extortion demand.
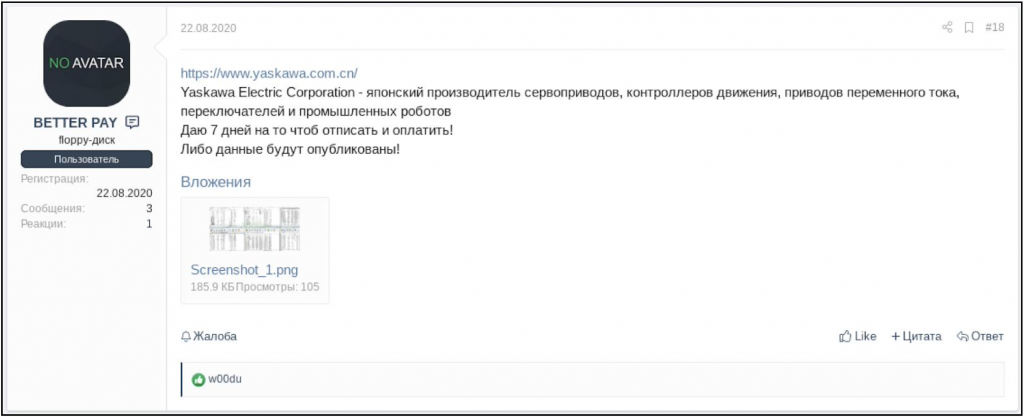
Image 1: Russian-language warning post by BETTER PAY.
On September 14, 2020, on the day that the LockBit blog was created, it posted two data breaches respectively affecting Yaskawa Electric Corporation and Overseas Express Shipping Company. As detailed in Gemini’s Ransomware report, ransomware teams use both the dark web and their own blogs in order to intimidate victims into paying ransoms. In addition to intimidating current victims, this tactic can also serve as a warning to future victims to show them the consequences of not paying a ransom.
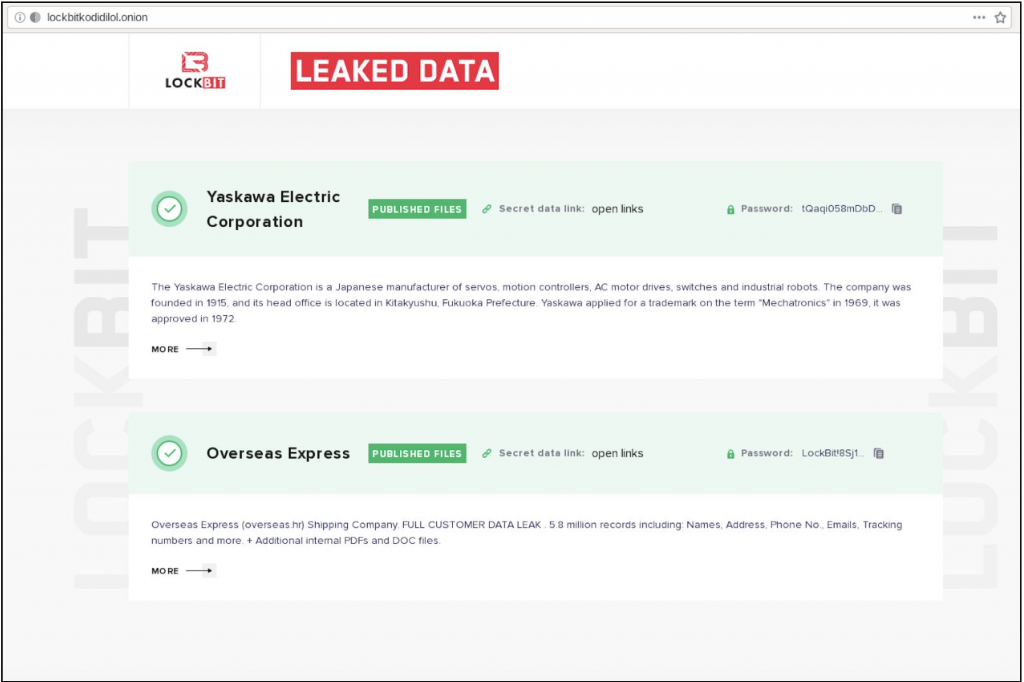
Image 2: The front page of LockBit’s blog.
LockBit uses the moniker “LockBIt” (with a capital “i”) on the second Russian-language dark web forum and creates very similar posts to the original forum mentioned above, some of which are actually identical. On January 17, 2020, both LockBit and LockBIt created posts on both forums to recruit affiliates to their ransomware team. As described in the Gemini’s Ransomware report, it is standard practice for large ransomware teams to recruit new members on the dark web forums.
The forums also provide a platform for cybercriminals to settle their grievances with one another and identify deals gone sour. As such, on September 2, 2020, on the first forum, cybercriminal actor “wexford” created a post demanding 10 Bitcoins from LockBit. In the post, wexford wrote that over the last four months they have been working with LockBit as an affiliate, identifying and encrypting various targets, however, they have not received ransom payments from their victims. Actor wexford pointed out that they initially thought that this was due to the fact that LockBit was not yet well known, and the victims were thus reluctant to pay. However, wexford now claimed that victims were having issues decrypting the files, which wexford purportedly explained to LockBit.
According to wexford, LockBit indicated that there was a bug in their system and that since August 23, network files were not getting properly encrypted. After this, wexford conducted an analysis of their previous “jobs” and noticed that the network files were not getting encrypted from the get-go; instead only local files were encrypted. Furthermore, wexford pointed out that the backups were not encrypted either. While all files appeared to be encrypted, most were not, which caused the decryption key to fail (since there was no encryption in the first place). wexford alleged that as victim companies discover this, LockBit would lose its negotiating leverage, and the companies could restore information from their network files or backups.
It appears that even the larger ransomware teams can have issues with data encryption. Usually, ransomware teams rely on two factors when conducting a ransomware attack. After gaining access to an organization, the cybercriminals will try to download the database from the organization, which can later be used as leverage, as was the case with Yaskawa Electric Corporation. The second portion of the ransomware attack is the encryption of the victim’s network, which would create a work stoppage for most organizations. Cybercriminals then request a ransom payment for a decryption key, which may be provided upon the successful payment. There could, however, be issues with decrypting the systems, as wexford pointed out in their complaint.
It is worth noting that cybercriminals do not always immediately divulge the fact that the victim’s database was downloaded. They sometimes only do so after the payment for decryption has been made, which allows the cybercriminals to double dip, first receiving a payment for the decryption key, and then later demanding a second payment for the database. If victims do not pay up, cybercriminals can threaten the victim to post the database for sale or even for free in the dark web. The databases could contain proprietary data, such as information on technology or research, or information on their clients, or even customer PII. It is also worth pointing out that in some cases ransomware attacks can be used as a cover for espionage and the main target is the database itself; these circumstances often do not include a demand for a second payment. A more detailed description of various tactics that are used by cybercriminals can be found in Gemini’s aforementioned Ransomware blog post.
With the addition of a public blog, LockBit joins the likes of other ransomware teams that have the same platforms to intimidate victims, promote their capabilities, and offer compromised data. This type of blog is yet another intimidation tool that these teams use and provides more leverage over their victims. Although data on the two victims has been posted, the success of LockBit’s encryption remains unclear. As was indicated by wexford, it appears that earlier ransomware attacks did not achieve their desired results, and as such, some of the victims may have escaped with no significant damage to the company. Additionally, the aggressive means by which LockBit threatened their latest victim and the subsequent posting of their database for free could indicate a failed encryption attempt and a desperate attempt to display their resolve and deter other victims from refusing to pay. Regardless of the successes and failures of LockBit, Gemini Advisory assesses with high confidence that the ransomware threat is likely to be persistent and will continue to threaten a wide range of companies.
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.