
In late 2019, the popular e-commerce platform Volusion was compromised in a Magecart attack. While Magecart attacks are relatively common, the scale of the Volusion attacks is far greater than that of previous incidents. The breach reportedly occurred between September 7 and October 10, 2019; while some reports claimed that the breach affected up to 20,000 online stores, 6,589 were confirmed to be connected to the compromised domain.
According to Trend Micro, the attack began on September 7 and impacted merchants with e-commerce sites hosted on Volusion’s cloud platform. Malicious code was reportedly injected into a Volusion JavaScript library that closely resembled legitimate code but included a payment card skimmer to pass along card details to an exfiltration server. The exfiltration server’s name was “volusion-cdn[.]com,” which resembled the legitimate server’s name to camouflage the illicit activity.
While Magecart attacks that compromise targeted merchants’ e-commerce platforms directly are common and often effective, many cybercriminals instead attack a partner organization in order to compromise the supply chain. Supply-chain attacks are effective because they allow hackers to pivot into the target merchant’s systems from a business partner’s legitimate access point. ZDNet included the directory path of the malicious script, hxxps://storage[.]googleapis[.]com/volusionapi/resourcesp[.]js, which is loaded onto Volusion-based online stores from the /a/j/vnav[.]js file.
Gemini Advisory determined that the script was dynamically injected into target pages and exfiltrated customer payment card data and names, including some additional personally identifiable information (PII) such as customer phone numbers. Analysis indicates that the compromises dated back to September 11, 2019, and on October 10 all 6,589 infected domains were cleared of malicious scripts.
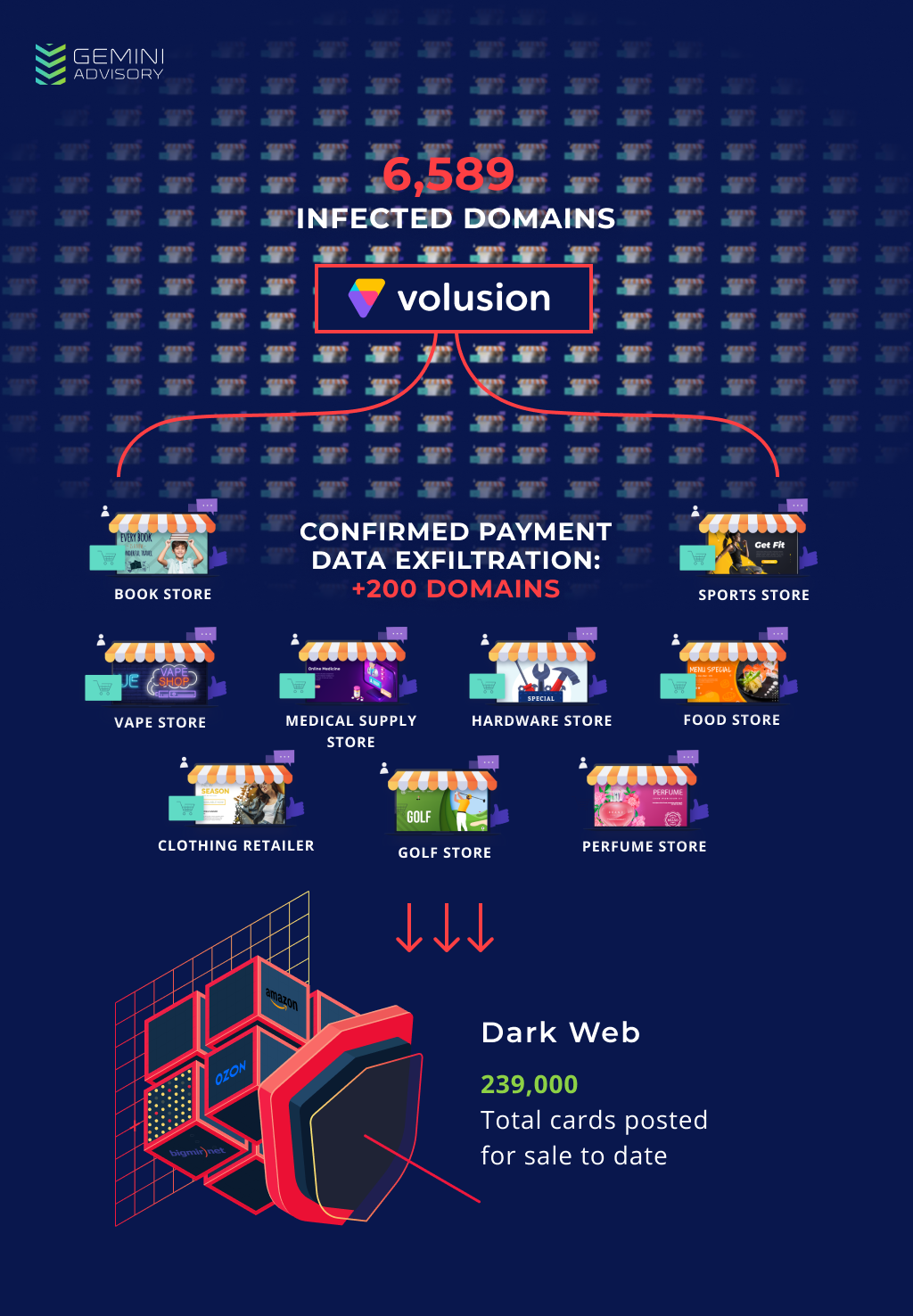
No compromised records from Volusion had appeared in the dark web directly after the incident. However, Gemini Advisory discovered over 239,000 compromised Card Not Present (CNP) records offered for sale in the dark web from November 2019 to the present. The records came from hundreds of different merchants; several hundred have been identified as of this writing. It affected a variety of industries, from sanitation (Marine Sanitation & Supply) to sports equipment (Sunshine Golf) to monster trucks (Monster Jam Store). These stores were listed among the 6,589 merchants referenced above, and their exposure window was between September and early October 2019. This aligns with Volusion’s exposure window.
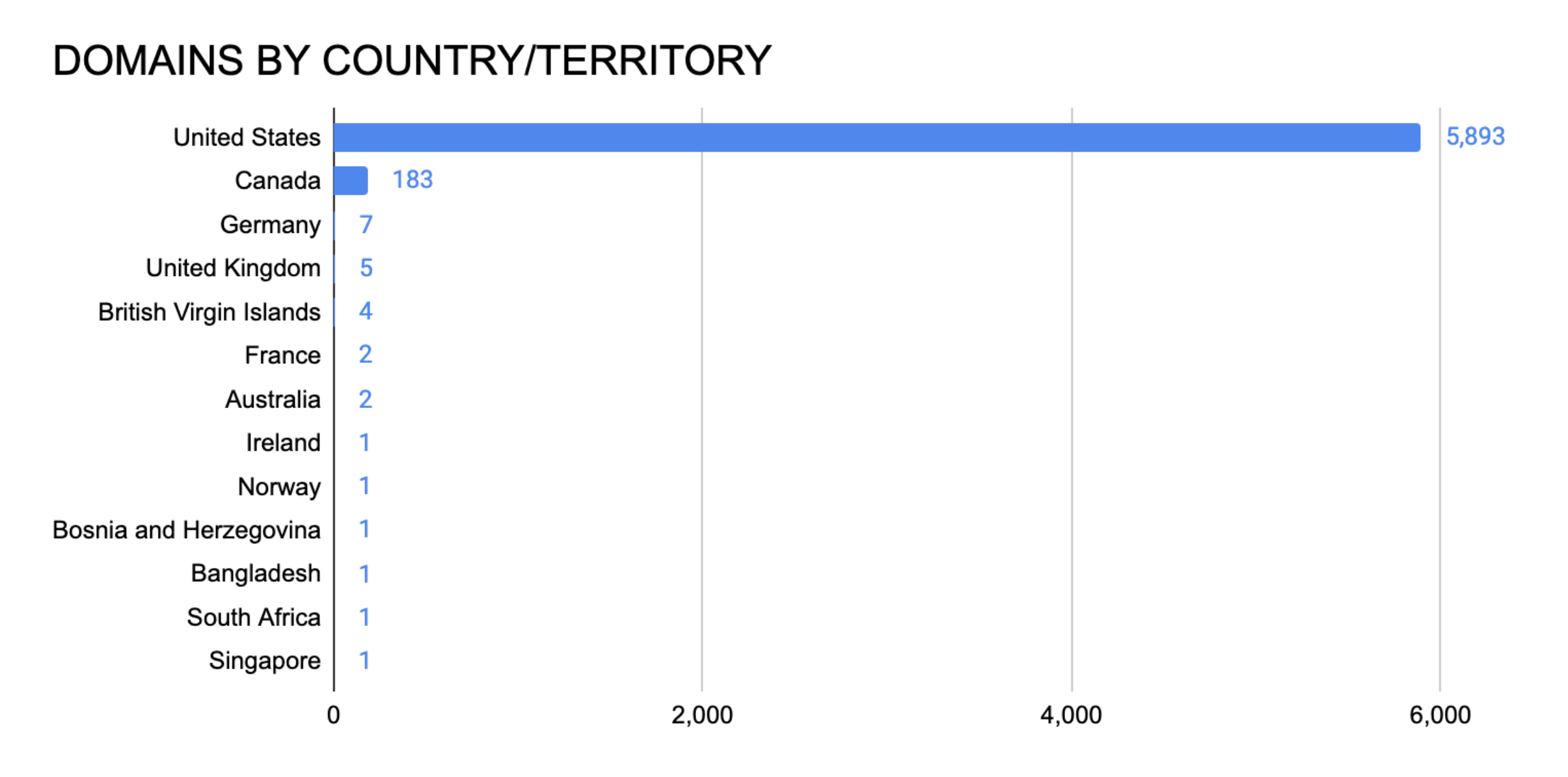
These records were 98.97% US-issued, with the next-largest issuer countries comprising only several hundred records each. This aligns with the merchants confirmed to be compromised since they primarily service US clients. It also aligns with the distribution of countries in which the 6,589 domains are registered.
As of this writing, fraudsters have generated $1.6 million USD in revenue from these stolen payment cards. The average CNP breach affecting small to mid-sized merchants compromises 3,000 records; scaling this figure to the 6,589 merchants using Volusion affected by this breach, the potential number of compromised records is up to nearly 20 million. Given this figure, the maximum profit potential would be as high as $133.89 million USD. The overwhelming and continually rising dark web demand for CNP records indicates a staggering profit potential for the perpetrators of this security incident. As more records make their way to the dark web and more merchants are confirmed to have been compromised via Volusion, the full extent of what is likely to be one of the largest and most wide-ranging supply-chain breaches to date will become clear.
If you believe this incident may have impacted your organization, you may contact us /##section-contact-us for complimentary exposure analysis.
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.