
Russian media reported that the Russian Federal Security Service (FSB) arrested 30 members of a hacker ring on March 20, 2020. These members were scattered across 11 regions of Russia and included citizens of Ukraine and Lithuania. According to the Russian media, the hackers specialized in selling compromised debit and credit cards stolen from both Russian and foreign citizens. During the arrest, authorities uncovered over $1 million USD, 3 million rubles, gold bars, computers, servers that were used to host dark web marketplaces, counterfeit ID cards (including Russian passports and government IDs), and weapons. Footage of the arrests can be found here:
Russian media reported that this hacker ring operated more than 90 dark web markets. While it did not indicate that any of these marketplaces were taken offline, this is standard practice for certain types of arrests, including those conducted by Russian law enforcement, which often keeps information-sharing to a minimum. Around the same time as these arrests, Gemini noted that a popular dark web marketplace known as BuyBest, as well as its mirrors, went offline.
Furthermore, an administrator on an elite Russian-language hacking forum posted the news article of the arrests on the forum. This actor added that Alexey Stroganov (AKA “Flint24”) was among the arrested hackers and that this actor was associated with GoldenShop; all the marketplaces associated with him are purportedly “locked.” BuyBest and GoldenShop are mirror markets, meaning that they sell compromised credit card information from the same sources and are oftentimes operated by the same groups of criminals. This indicates that the hacker ring operated BuyBest and its mirrors, which have since been taken offline by Russian law enforcement. Stroganov’s arrest has been officially confirmed by the Moscow General Judicial Court.
Both the BuyBest and GoldenShop marketplaces are large, top-tier marketplaces. GoldenShop has operated as far back as early 2013. Analysts have identified multiple mirror markets that sold credit card data similar to that of BuyBest/GoldenShop, and estimate that the number of markets indicated in the news article includes those mirrors, as well as older marketplaces that are no longer functional. Gemini has identified 47 potential mirrors that, although interconnected, appear to be run by different administrators.
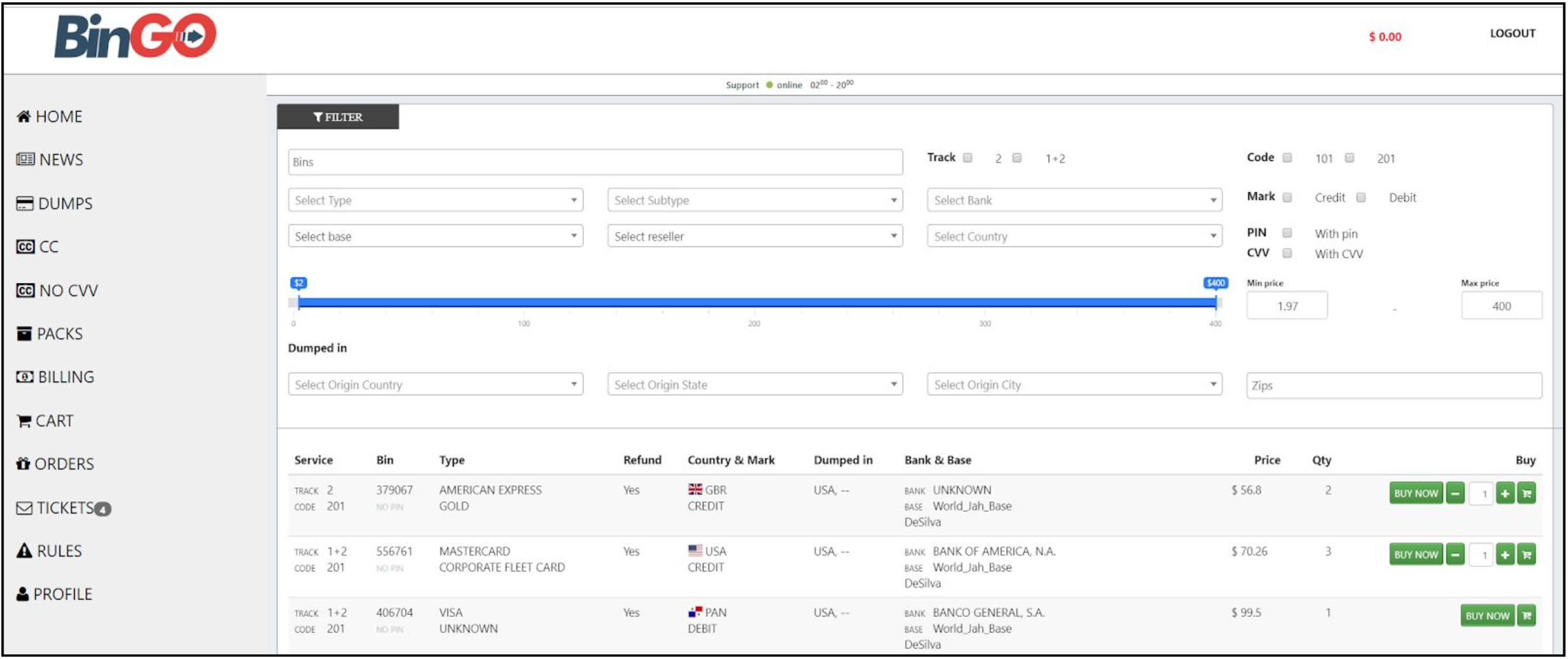
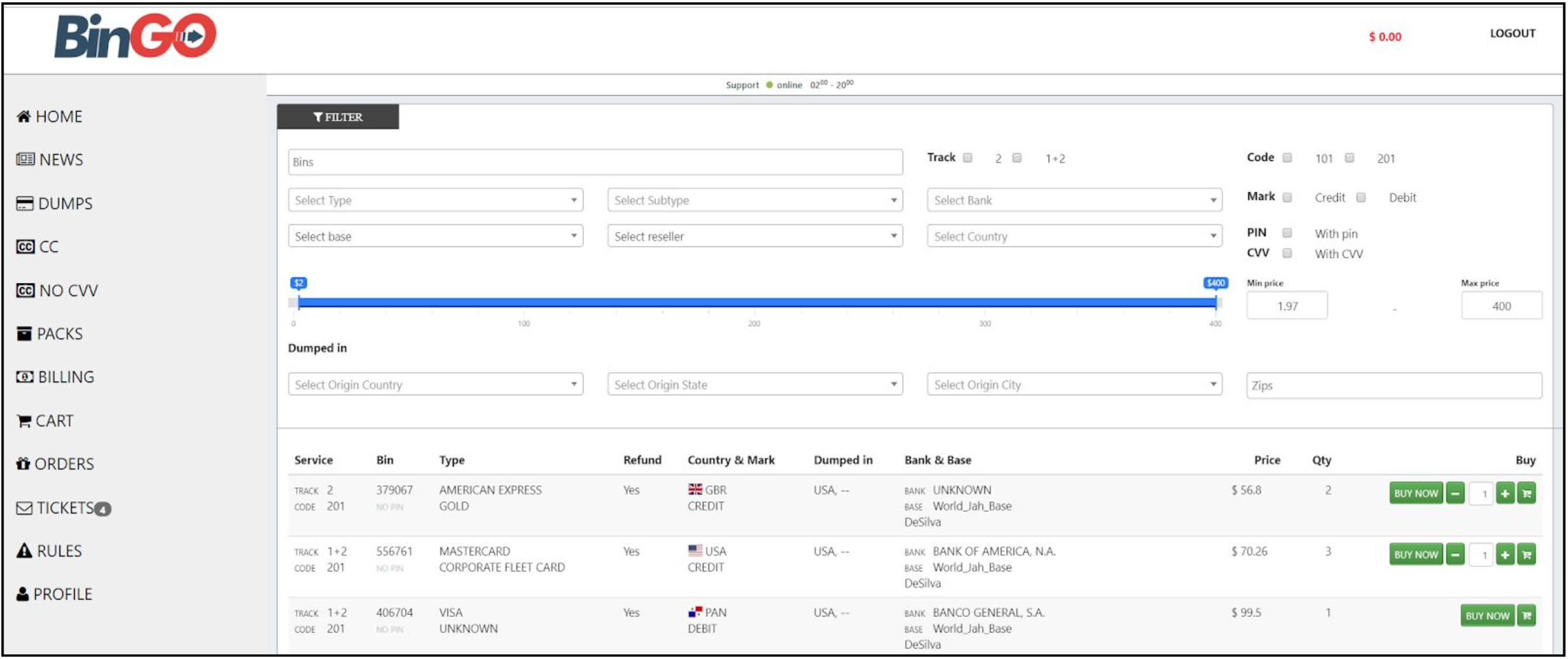
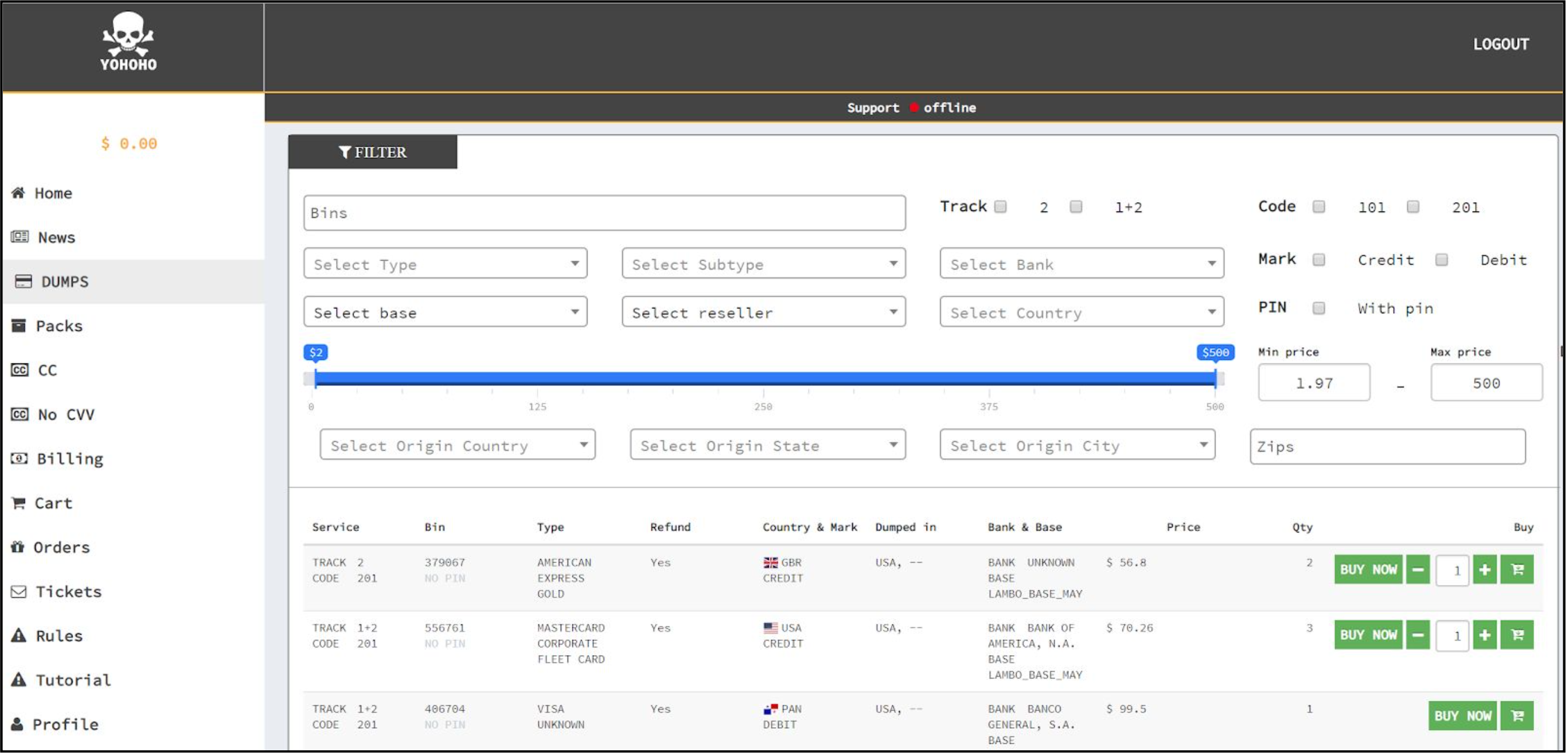
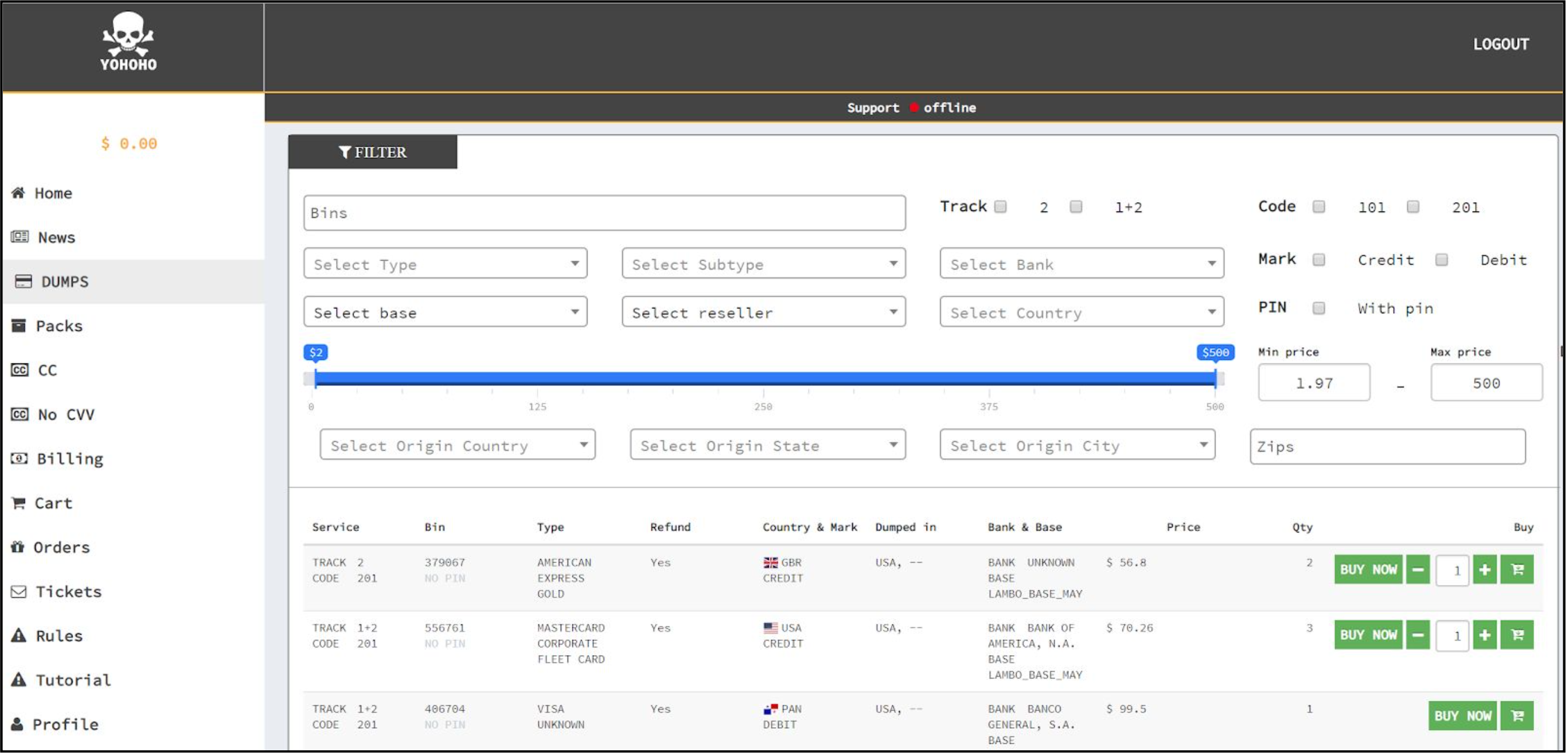
The BuyBest/GoldenShop first appeared in 2013 and appears to have generated massive profit for its administrators. Gemini Advisory estimates that between 2013 and 2020, this criminal enterprise earned up to $70 million, approximately $18 million of which was likely paid to the marketplace owners, and another $52 million to the suppliers of the compromised data. The marketplace was known for selling phished data, which often included Social Security numbers (SSNs), dates of birth (DOBs), victim IP addresses and User Agents.
BuyBest was responsible for selling millions of compromised Card Present (CP) and Card Not Present (CNP) cards over its lifespan. Some of the compromised records came from multi-location breaches at victim merchants such as Caribou Coffee and Russell Stover.
One of the more unique items about this marketplace is the presence of a dedicated forum. Most markets advertise their services in the general underground dark web forums; however, a select few run their own forum. Marketplace administrators operated a forum called CarderBazar as a platform to advertise the GoldenShop/BuyBest and all of its mirrors, as well as to advertise the sales of new compromised card data. CarderBazar also had additional sections focusing on illegal cyber activities.
According to Gemini sources, the head of the hacker ring was an individual named Alexey Stroganov (operating under the moniker Flint24), who was arrested along with the rest of the organization’s members. Information on his arrest can be verified via Moscow General Judicial Court filing and has been reported on multiple top-tier Russian-language dark web forums. In 2006, Alexey Stroganov was found guilty of cybercrimes and was sentenced to six years in prison. He served two and was released in 2008. He also made an appearance in a book by Belorusian hacker Sergey Pavlovich, How To Steal A Million: Memoirs of a Russian Hacker, who wrote that Flint24 was a moderator of a top-tier Russian-language forum called carder[.]org and manufactured counterfeit credit cards. After his release, Stroganov (Flint24) continued to be a member of Russian-language dark web forums. His presence was far more discreet following his initial arrest and he did not reveal any of PII or contact details; his operational security (OPSEC) likely improved due to his arrest. On multiple occasions, Flint24 endorsed the credit card marketplace BuyBest on another top-tier Russian-language dark web forum.
There is a long-standing belief among the security community that certain governmental agencies in Russia cover hackers who are operating in the Russian territory. According to this theory, there are certain Russian hackers who are unable to leave the country because they are wanted for cybercrimes by foreign governments. This belief is widespread among cybercriminals as well; because of this, much of the Russian cybercriminal underground operates under an unwritten rule: if you don’t hack your own people (Russian citizens), the government will let you operate, as long as you share the profits with them. As such, hackers working under these conditions likely have wide access to resources, such as receiving government IDs and counterfeit passports. BuyBest appears to have subscribed to these rules as well, and prohibited the sale of Russian card data.
In this environment, it is highly unusual for Russian law enforcement to arrest notable Russian hackers, especially those who do not target large numbers of Russian victims. The reason for this anomalous event remains unclear; while cybercriminals across the dark web have offered speculative explanations, there is no definitive indication as to whether this arose from cybercriminal rivalries, transgressions of an agreement between these hackers and Russian officials connected to law enforcement, or something else entirely.
While the BuyBest marketplace did not allow the sale of compromised Russian-issued payment cards, it remains unclear if Stroganov and the other hackers targeted Russian businesses. If they did so, the data may have appeared on one of the over 90 purported mirrors, which could have drawn the attention of law enforcement.
Another possible explanation is a conflict with another group of hackers. Russian-language payment card marketplaces have engaged in aggressive sabotage before, as is evident by the 2019 hack of the BriansClub dark web marketplace. The cybercriminal underground concluded that the hackers ran another rival market called Mr.Green, and stole compromised card data from BriansClub and leaked them to the media to undermine the cards’ validity and the marketplace’s reputation. It is possible that the BuyBest takedown and arrest of 30 hackers was an escalation in a similar rivalry between Russian cybercriminal rings.
Based on the information provided in the news reports, as well as intelligence gathered by Gemini, analysts assess with a high degree of confidence that the arrested individuals were involved in the operation of the dark web marketplace BuyBest/GoldenShop and its mirrors. This information aligns with Gemini’s research findings, which point to multiple individuals operating these marketplaces, which in turn corresponds with multiple individuals being arrested. Furthermore, information that they were operating over 90 markets also correlates with the numerous mirrors available for BuyBest/GoldenShop, and Gemini observed that these marketplaces went offline parallel to the arrests. Gemini Advisory assesses with a high degree of confidence that one of the individuals in charge of this network is Alexey Stroganov due to his arrest, extensive record of cybercriminal activity, and the well-known admin of the elite hacking forum naming him as the owner of the GoldenShop.
| Name (Cyrillic) | Name (Latin) |
|---|---|
| Строганов А.Т | Stroganov A.T. |
| Бобин А.С. | Bobin A.S. |
| Юшковский А.А. | Yushkovskiy A.A. |
| Шувалов А.В. | Shuvalov A.V. |
| Малинин М.А. | Malinin M.A. |
| Селиванов Г.В. | Selivanov G.V. |
| Галкин А.В. | Galkin A.V. |
| Карпунин С.В. | Karpunin S.V. |
| Федотов И.О. | Fedotov I.O. |
| Светличный Л.И. | Svetlishniy L.I. |
| Мерлин Э.А. | Merlin E.A. |
| Васильев Р.Р. | Vasilev P.P. |
| Синицын А.В. | Sinitsin A.B. |
| Белай В.В. | Belay B.B. |
| Ахметов В.А. | Akhmetov B.A. |
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.