
In 2018, news of payment card breaches and compromises has become routine, and it does not faze cardholders as much as it did a few years ago. This culture has become too common in the West, but where does this leave the rest of the world? In one of our previous blogs, “Card Fraud on the Rise, Despite National EMV Adoption,” we discussed just how overwhelming the fraud is in the United States while only shining a small light onto the rest of the world. In this blog, we are going to broaden our gaze and focus on levels of compromised payment cards in the East Asia region, and specifically the country of Japan.
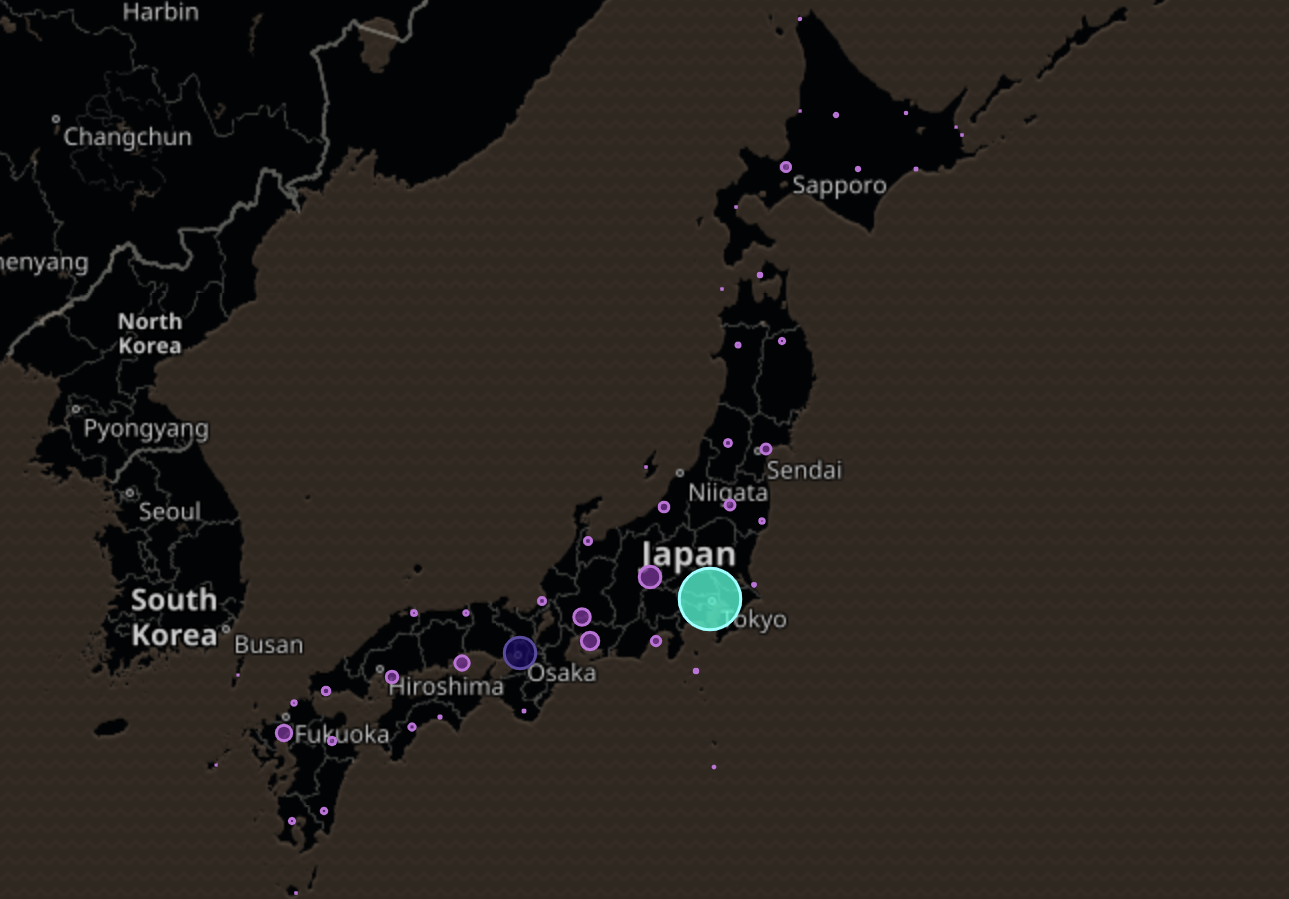
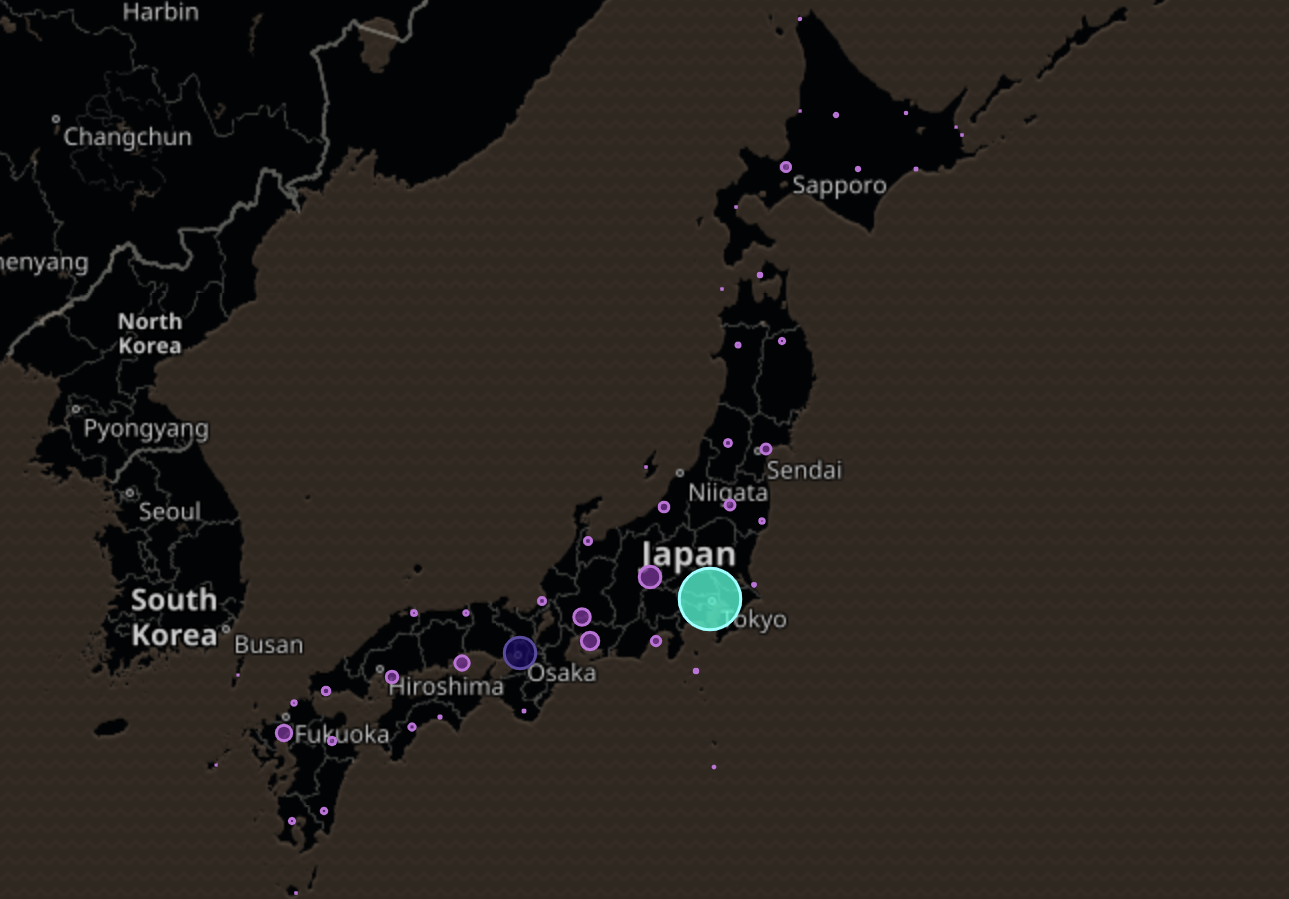
Based on the proprietary Gemini Advisory telemetry data collected from various dark web sources over several years, we have determined that in 2018, nearly 1.4 million cards were compromised in the East Asia region. Of those, 57% (800,617) were Card Not Present (CNP) records, likely compromised through various e-commerce breaches such as Huazhu Hotels Group, Cathay Pacific, Prince Hotels, and Hong Kong Broadband Network. Furthermore, 42% (595,335) of the total stolen cards were Card Present (CP), likely compromised through card-sniffing and point-of-sale (POS) breaches of businesses. In both cases, the cards were likely to have been compromised in the East Asian region as well as when cardholders purchased goods and services via foreign e-commerce platforms or when using compromised POS terminals while traveling abroad.
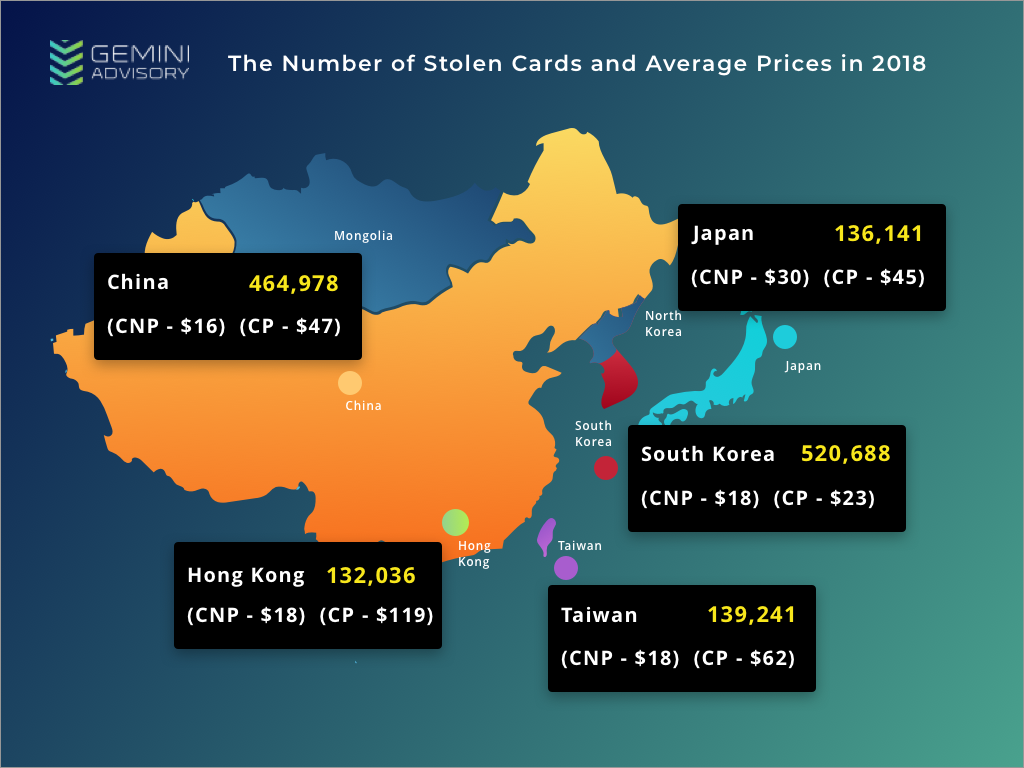
Compared to Gemini Advisory telemetry data collected in 2017, the East Asian region experienced a nearly 100% increase in compromised cards in 2018. The analysis of this region identified nearly 1.4 million compromised cards for sale in the dark web; of those cards, 37% (520,688 cards) were from South Korean cardholders. Unlike the rest of the East Asian countries, South Korea predominantly fell victim to CP fraud with nearly 390,000 payment cards stolen from POS terminals. The compromised cards were EMV-enabled and primarily compromised in South Korea, although some instances occurred in the United States, China, and other countries around the world. Of the 390,000 compromised payment cards, over 74% (290,000 cards) were compromised prior to South Korea’s end of July deadline for retailers to shift to exclusively chip cards. The rest of the East Asian countries align with the trend of predominantly CNP/e-commerce compromises since implementing EMV card technology and EMV-enabled POS systems make it more difficult to conduct CP fraud.
Despite the overarching trend of increased fraud in East Asia, Japanese compromised card levels decreased by over 100% in 2018, largely due to what appears to have been a massive upload of 280,000 Japanese CNP payment records posted for sale in January of 2017. This strongly implies a potentially undisclosed breach of one or more Japanese e-commerce sites at the end of 2016.
Between January 1 and December 31 of 2018, 136,141 Japanese cards were compromised and posted for sale in various dark web marketplaces. The cards were split between 97,095 CNP records with a median cost of $30 USD per card, and 39,046 CP records with a median cost of $45 USD per card. During the monitored period, Gemini Advisory identified an out-of-pattern spike in records added to the dark web in November and December of 2018; December exhibited a 1,859% increase in added Card Not Present (CNP) records compared to the January through October average. This spike of newly added records appeared to run parallel to a growing demand in Japanese-issued cards between November and December. Through open source research, Gemini Advisory identified that during the aforementioned timeframe, a number of Japanese cardholders published various complaints regarding a newly released Japanese payment app called PayPay. Cybercriminals likely utilized this app as a means of monetizing stolen Japanese payment cards, as well as compromising and monetizing the credentials of existing legitimate PayPay users.
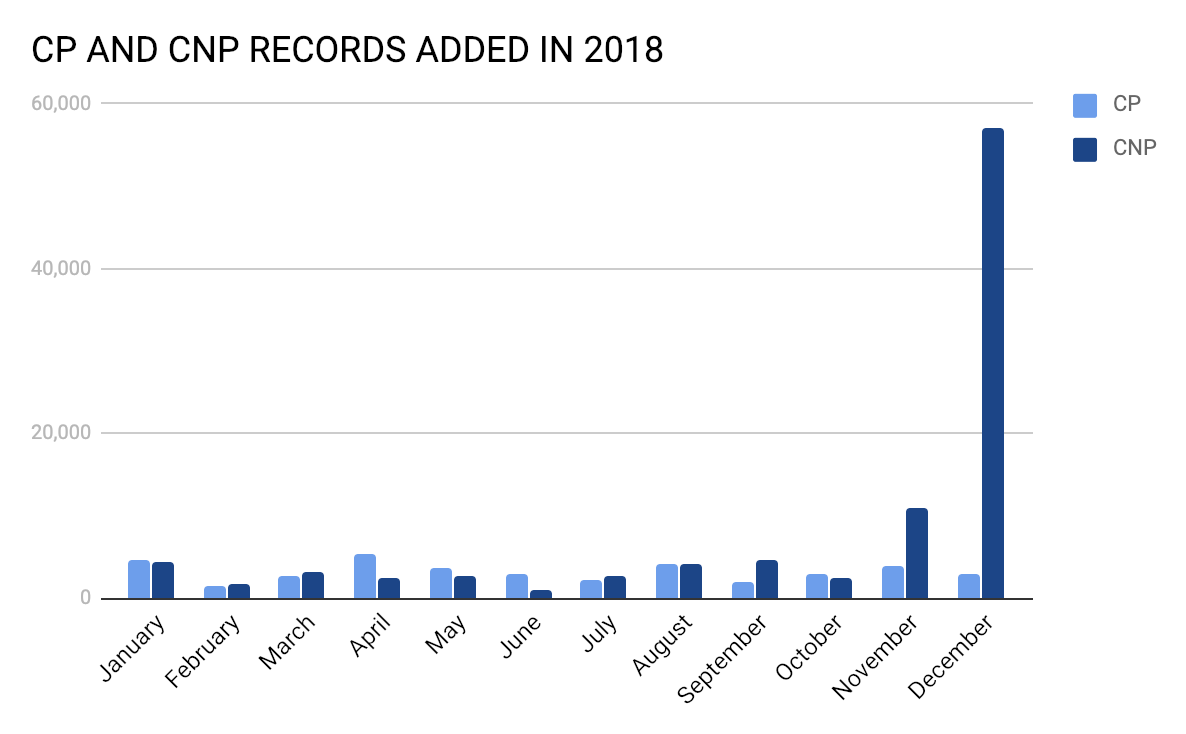
Based on the overlapping timeframes between PayPay fraud and the spike in Japanese payment cards added to dark web marketplaces between November and December 2018, Gemini Advisory assesses with moderate confidence that these two events are related.
PayPay was founded on June 15, 2018 and has risen to prominence in Japan following a bold campaign to recruit new users. It is a payment app designed to streamline cashless transactions and is compatible with both iPhone and Android devices. The company is backed by Softbank Group and Yahoo! Japan Corporation, and also collaborates with Paytm, India’s largest payment service provider, to integrate QR (Quick Response Code) technology into its systems.
To conduct transactions with PayPay, a user must register either through the app itself or with a Yahoo! Japan ID. An authentication code is sent to the user’s device via SMS, and after verification, the user must enter their bank account to add funds to their PayPay account or enter their payment card information to directly purchase items. PayPay is compatible with a select number of stores, all of which are large companies as of this writing. Payments are completed by scanning a QR code or displaying a bar code for the vendor to read.
Promotion
In order to increase its user base, on December 4 PayPay launched a promotion offering to reimburse users 20% of purchases up to 100,000 yen ($880 USD as of December 4). This promotion, backed by Softbank for up to 10 billion yen ($88 million USD as of December 4), was originally intended to run through the end of March; its popularity instead drained the entire fund in 10 days.
However, this successful promotion also heralded a spike in payment card fraud. While Japan sees an average of 2,909 compromised CNP records added to the dark web each month, December saw 57,000 compromised CNP cards, a 1,859% increase. Not only did PayPay users report fraudulent transactions on their payment cards, but cardholders who had never downloaded the PayPay app also fell victim. This appears to be largely because PayPay did not set a limit on the amount of incorrect Card Verification Value (CVV Number) entries a user can enter. This made the app vulnerable to brute forcing attacks.
Following public backlash against PayPay’s insufficient security measures, the company implemented a limit to incorrect CVV entries on December 21, 2018 as a provisional measure to combat payment fraud. Additionally, PayPay set a new purchase ceiling of 20,000 yen ($182.44 USD) per day and 50,000 yen ($460.58 USD) per 25-day period, as of January 21. Payments above the 50,000 yen 25-day ceiling now use 3D Secure, an extra authentication step for the consumer during purchases. It is noteworthy that 3D Secure is not compatible with all banks, and incompatible cards will be validated without this layer of authentication. Purchases over the ceiling also require an identity card for verification, which can consist of a driver’s license, passport, number card, special permanent resident certificate, residence card, health insurance card, or student card. After verifying a user’s ID, the 25-day limit becomes 250,000 yen ($2,302.92 USD).
The company has issued public statements promising a greater emphasis on security, with one spokesperson saying: “We regret putting too much emphasis on the convenience of customers and not doing enough to prevent wrongdoing.” While the limit on incorrect CVV entries, new purchase ceiling, 3D Secure, and the photo verification for payments above the ceiling are four such measures, it remains unclear whether other significant security flaws exist, how they may be exploited, and what proactive measures PayPay may take to preempt further fraudulent activity.
Relevant Cybercriminal Activity
Based on various dark web discussions, cybercriminals often sought to cash out Japanese CNP payment cards on EU and North American e-commerce platforms due to a lower fraud detection rate for transactions made outside of Japan. However, based on Gemini’s analysis of dark web marketplaces, the high demand for Japanese cards occurred parallel to the implementation of PayPay and its December promotions. The threat actors likely took advantage of this third-party payment app in order to monetize CNP payment card data at in-store locations in Japan that accept the PayPay QR code payment style. In addition to the monetization of compromised payment cards via the PayPay app, the criminals were also able to earn 20% back on all of their purchases during the promotion timeframe of December 4 to December 14.
This activity also indicates that the cybercriminals who purchased the CNP records and monetized them via PayPay had to be present at physical store locations in order to do so. This means that this activity was likely backed by various threat actors or criminal groups located in Japan rather than cybercriminals located in other foreign countries who often purchase goods via e-commerce platforms and reship them through a network of mules.
Gemini Advisory identified that after the implementation of incorrect CVV entry limits, 3D Secure, and a new spending ceiling, the number of Japanese payment card records added to dark web marketplaces has significantly declined. It is possible that the spike in compromised payment card information in the dark web was due to an e-commerce breach unrelated to PayPay, and that fraudsters simply used PayPay as another method to monetize their illicitly obtained payment card information. However, the dark web’s sudden rise in demand for Japanese payment cards and subsequent decline matches the timeline of PayPay’s promotion and later implementation of new security measures, lending credence to the assessment that these two developments are related.
The heightened dark web activity surrounding the PayPay breach is noteworthy because it disrupted Japan’s trend of declining rates of compromised payment cards. Any new technology that prioritizes ease of use and customer convenience over security can provide threat actors with an opportunity to breach or manipulate the system. With the exception of high-profile incidents such as this one, Japan remains an outlier in the East Asian threat landscape, and its more secure financial institutions appear to disincentivize cybercriminals from attempting to breach them instead of easier regional targets.
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.