
The invention of the EMV chip was one of the most significant developments in secure payment card technology. While payment cards had previously relied on the magnetic stripe (magstripe) to store information, fraudsters had been cracking this technology and cloning victims’ cards for years. To prevent fraudsters from placing illicit purchases with cloned payment cards, EMV chips encrypt the payment card data and the CVV (called iCVV for EMV-enabled cards). A new encryption key (also called a token or cryptogram) is generated upon each purchase for Card Present (CP) transactions. This token is generated by the interaction between the EMV chip and the card reader and applies only to that single transaction. Since the token cannot be repeated for an additional transaction, stealing it does not allow cybercriminals to place fraudulent transactions with a cloned EMV-enabled card. There is currently no compelling evidence that any cybercriminals have discovered a method of cloning this technology. EMV chips transformed the underground payment card economy, shifting most illicit markets towards Card Not Present (CNP) records; merchant compliance with regulations mandating EMV chip transactions correlate strongly with the presence of CP fraud in any given country.
However, new research indicates that there are other ways to bypass EMV technology and monetize these supposedly secure cards. An in-depth report by Cyber R&D Lab detailed a method of acquiring enough data through compromised EMV transactions to clone a payment card. This method leverages information from one technology (EMV chips) and converts it into another less-secure technology (magstripe), which allows fraudsters to rely on their familiar cloning techniques. Gemini will refer to this technique as EMV-Bypass Cloning.
Magstripes are particularly vulnerable because they do not encrypt the track 1 or track 2 data necessary to place a transaction. This lack of encryption made it easy for fraudsters to steal payment card data, and then equally easy to clone the card with this stolen data. EMV technology is more secure because it encrypts the payment card information stored on the chip during the transaction.
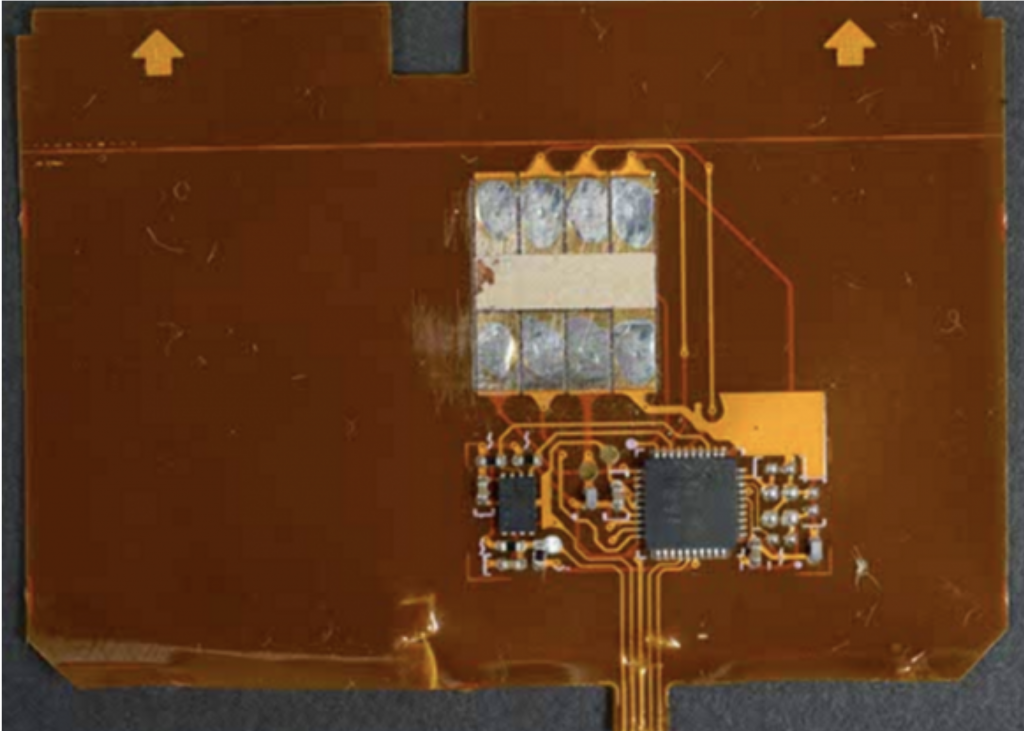
There are multiple ways for a cybercriminal to obtain the payment card data of EMV-enabled cards. The most popular method involves a “shimmer,” a physical device that a cybercriminal attaches to a point-of-sale (POS) terminal to collect payment data before passing it along to the POS terminal itself. This allows the fraudster to steal the card data while allowing the legitimate transaction to take place, which prevents the victim from realizing that their payment card information was compromised.
According to Krebs on Security, the data collected by shimmers cannot be used to clone a chip-based card, although it can be used to clone a magstripe card. While the data that is typically stored on a card’s magstripe is replicated inside the chip on chip-enabled cards, the EMV chip also contains an additional security component not found on a magstripe. That security component is the iCVV number, which differs from the CVV that is located on the magnetic stripe.
However, this layer of security is rendered useless if a financial institution does not check for the proper CVV number during a swipe transaction. Because of this loophole, a cybercriminal can take data from an EMV-enabled card and translate it into magstripe data. That criminal can clone the victim card, creating a fraudulent magstripe card using EMV data. Thus, EMV-Bypass Cloning allows them to bypass the chip’s extra layers of security and revert to an older, more reliable method of fraud.
Fraudsters can use such a cloned card the same way they would use a card cloned from a compromised magstripe transaction. They cause the EMV transaction to fail through one of several ways (e.g., not fully inserting the card into the card reader; covering the EMV chip with tape or superglue; etc.), and then they accept the cashier’s offer to swipe the card instead.
The viability of this technique depends upon a bank’s security posture. If a bank mandates that every card security code is verified upon each card transaction, the technique will fail. However, the Cyber R&D Lab researchers suspected that some banks do not verify the iCVV or CVV for all transactions, which would leave the card vulnerable to exploitation through the method detailed above. To test this theory, they used both an app and a physical card reader to record the card data. They chose 11 cards from 10 banks (including both Mastercard and Visa cards) from US, UK, and EU issuer countries to attempt their experiment.
The researchers used several different types of card readers to interface with all 11 cards, and were able to harvest data from four of them. With the data from these four cards, they created cloned magstripe cards and successfully placed transactions. These transactions would have failed if a simple check for data integrity occurred during payment.
Cyber R&D Lab did not specify which bank/card issuer combinations were most vulnerable to this technique. The issues appear to be twofold: first, the card data could be harvested from four of the 11 cards, which implies a security shortfall from the card manufacturer or the issuer bank’s encoding process for the card data. Second, the banks did not verify that the correct CVV code (as opposed to the harvested and substituted iCVV code) was used in magstripe transactions.
This experiment validates the theory that EMV data can be converted into magstripe data and thus support fraudulent CP transactions. Lack of proper encryption or verification of data integrity appears to enable this technique. If dark web forums circulate EMV-Bypass Cloning guides, it may undermine EMV cards’ security and raise demand for them in the cybercriminal marketplaces, launching a new wave of cyberattacks on a type of transaction previously assumed to be safe.
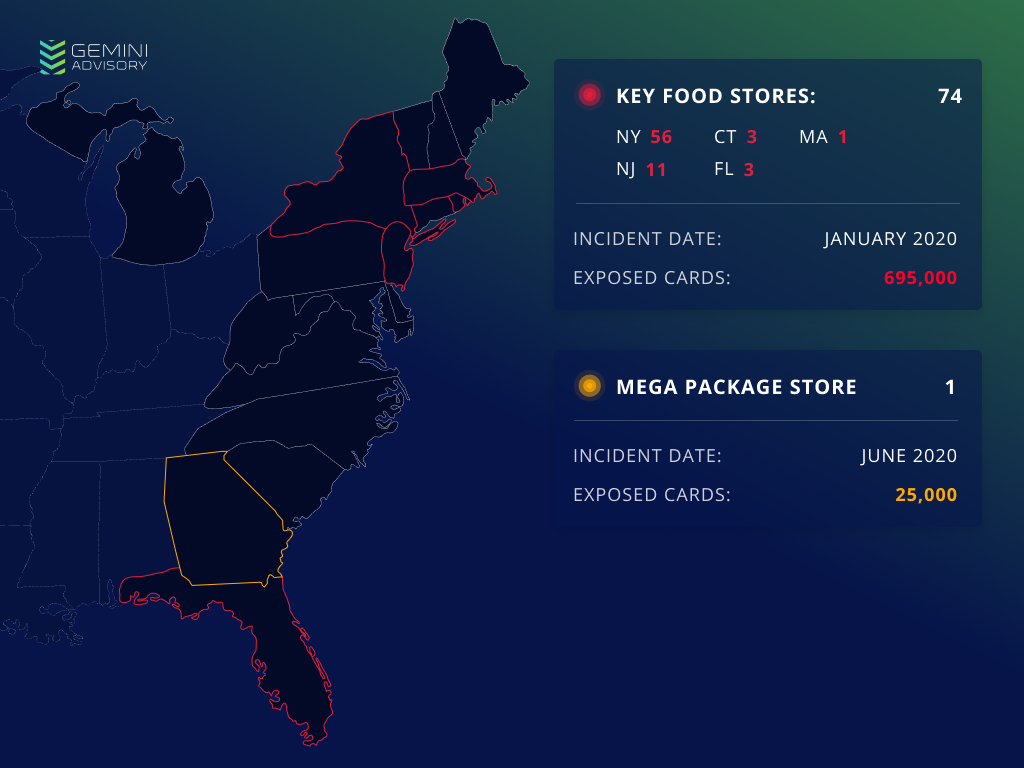
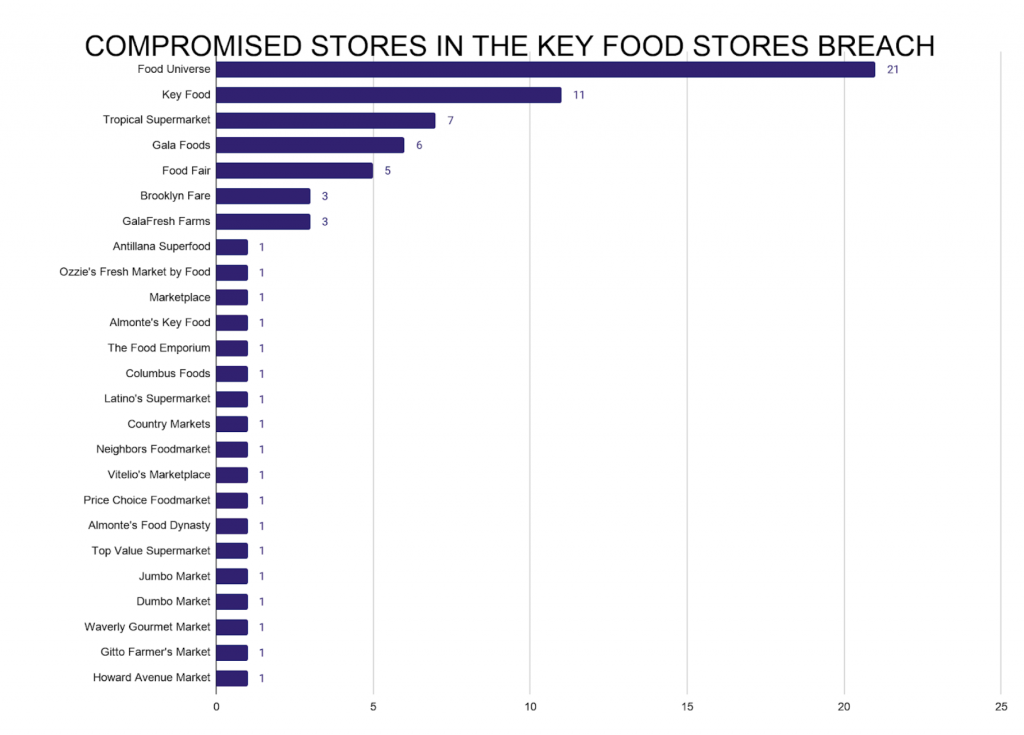
Gemini data indicates that this technique is already in use among the cybercriminal underground. On January 16, 2020, Gemini identified a massive breach of Key Food Stores Co-Operative Inc., a supermarket chain cooperative with affiliates largely (but not exclusively) in the northeastern United States. Many of the supermarkets in this cooperative use point-of-sale (POS) terminals that support EMV transactions with distinct network security systems. The payment cards stolen during this breach were offered for sale in the dark web. Shortly after discovering this breach, several financial institutions confirmed that the cards compromised in this breach were all processed as EMV and did not rely on the magstripe as a fallback. Analysts had speculated that payment card data on the EMV chip was compromised and repurposed for cloned magstripe cards, and Cyber R&D Lab’s recent revelations provide further clarity into the likely attack vector.
Gemini additionally identified a breach of Mega Package Store, a US wine and liquor store based in the state of Georgia, on June 29, 2020. The stolen cards were also compromised during EMV-enabled transactions. The same attack vector would explain how the attackers managed to compromise and then monetize cards from EMV transactions.
While Cyber R&D Lab demonstrated how EMV-Bypass Cloning can take place with physical access to targeted cards, and Krebs on Security shed further light onto shimmers as a means to steal card data, it is unlikely that the cybercriminals responsible for the Key Food Stores breach physically installed shimmers onto each store location’s POS terminals. Given the extreme impracticality of this tactic, they likely used a different technique to remotely breach POS systems to collect enough EMV data to perform EMV-Bypass Cloning.
Gemini notified law enforcement of both breaches shortly after discovering them. Key Food Stores first announced the breach on March 2, and later released an updated statement on July 16 reporting that even its EMV transactions had been compromised. While the public statement claimed that “we believe only the card number and expiration date would have been found by the malware (but not the cardholder name or internal verification code),” Gemini has observed additional data exposed in the dark web that includes the iCVV, which can be substituted for a CVV in magstripe data to clone a card. This cloned card can place fraudulent transactions depending on the bank’s verification process, as referenced above. The malware, therefore, must have harvested magstripe-equivalent payment card data from EMV-enabled POS terminals. A similar strain likely also infected Mega Package Store. Proper iCVV verification from banks should thwart this technique.
In the breaches of Key Food Stores and Mega Package Store, major supermarkets have lost over 720,000 compromised cards. Since not all card-issuer banks verify the magstripe data upon each swipe transaction to ensure that it was not stolen and translated from the EMV chip, some of these records are viable for EMV-Bypass Cloning. This is encouraging to cybercriminal buyers seeking to cash out these records, which in turn prompts hackers to continue targeting merchants that comply with EMV implementation standards.
EMV technology may have changed the underground market for CP records, but EMV-Bypass Cloning has opened the door for cybercriminals to sidestep the central security features of EMV chips and channel a new source of CP cards back into the underground CP market. The compromised merchant locations from the Key Food Stores breach are listed in Appendix A, while the Mega Package Store data is in Appendix B.
While analysts have not found dark web chatter highlighting EMV-Bypass Cloning or malware capable of capturing such data from EMV-enabled POS devices, the Key Food Stores and Mega Package Store breaches came from two unrelated dark web sources. This indicates that the technique used to compromise this data is likely spreading across different criminal groups using advanced operational security (OPSEC).
While EMV chips had proved impossible for cybercriminals to crack for many years, EMV-Bypass Cloning has undermined the security of the most reliable card technology on the market. Cybercriminals appear to have already used the technique in the wild to conduct breaches at scale and tap into a new source to feed the CP card dark web market. However, since EMV-Bypass Cloning merely leverages encryption and verification policies rather than compromises EMV technology itself, the solution lies in these same policies.
The four cards vulnerable to this technique in Cyber R&D Lab’s experiment had no verification process checking that the data inputted as magstripe data actually originated as magstripe data rather than being translated from an EMV chip. A higher verification standard involving data checks would raise the threshold of access and undercut fraudulent card use. EMV-Bypass Cloning is dangerously effective, but through policy review and higher verification standards, card providers and financial institutions can close the security gaps that this method exploits and restore the security integrity of EMV chips.
| Location | State | City | Address | Exposure Time Period |
|---|---|---|---|---|
| Almonte’s Food Dynasty | NY | Brooklyn | 1525 86th Street | 04/08/2019 – 01/24/2020 |
| Almonte’s Key Food | NY | Brooklyn | 5101 Avenue N | 04/08/2019 – 01/24/2020 |
| Antillana Superfood | NY | Bronx | 1339 Jerome Avenue | 01/08/2019 – 04/17/2020 |
| Brooklyn Fare | NY | Brooklyn | 200 Schermerhorn Street | 04/09/2019 – 01/24/2020 |
| Brooklyn Fare | NY | New York | 666 Greenwich Street | 03/07/2019 – 01/24/2020 |
| Brooklyn Fare | NY | New York | 431 W 37th Street | 04/09/2019 – 01/24/2020 |
| Columbus Foods | NY | New York | 81 West 104th Street | 03/08/2017 – 02/27/2020 |
| Country Markets | NY | Eastchester | 344 White Plains Road | 03/31/2019 – 01/24/2020 |
| Dumbo Market | NY | Brooklyn | 66 Front Street | 03/31/2019 – 01/24/2020 |
| Food Fair | NY | Bronx | 1065 E. 163rd Street | 04/07/2019 – 01/24/2020 |
| Food Fair | NY | Bronx | 656 Castle Hill Avenue | 03/31/2019 – 01/24/2020 |
| Food Fair | NY | Spring Valley | 175 E. Central Avenue | 03/31/2019 – 01/24/2020 |
| Food Fair | NJ | Newark | 323 Mount Prospect Avenue | 03/31/2019 – 01/24/2020 |
| Food Fair | NJ | Paterson | 956 Market Street | 03/31/2019 – 01/24/2020 |
| Food Universe | NY | Bronx | 119 Einstein Loop | 03/13/2019 – 01/24/2020 |
| Food Universe | NY | Bronx | 111 Dreiser Loop | 03/13/2019 – 01/24/2020 |
| Food Universe | NY | Bronx | 2061 Bartow Avenue | 03/19/2019 – 01/24/2020 |
| Food Universe | NY | Bronx | 3942 White Plains Road | 01/27/2017 – 02/14/2020 |
| Food Universe | NY | Bronx | 148 East Burnside Avenue | 01/27/2017 – 04/17/2020 |
| Food Universe | NY | Bronx | 82 W. Kingsbridge Road | 10/18/2018 – 03/04/2020 |
| Food Universe | NY | Bronx | 2358 University Avenue | 01/05/2019 – 04/02/2020 |
| Food Universe | NY | Bronx | 60 W. 183rd Street | 12/19/2018 – 02/16/2020 |
| Food Universe | NY | Bronx | 1334 Louis Nine Boulevard | 03/29/2019 – 01/24/2020 |
| Food Universe | NY | Brooklyn | 1038 Rutland Road | 01/27/2017 – 02/13/2020 |
| Food Universe | NY | Brooklyn | 405 Remsen Avenue | 01/26/2017 – 03/03/2020 |
| Food Universe | NY | Brooklyn | 243 Schenectady Avenue | 03/12/2019 – 01/24/2020 |
| Food Universe | NY | Brooklyn | 4118-22 Third Avenue | 01/04/2019 – 02/14/2020 |
| Food Universe | NY | Brooklyn | 416 Crescent Street | 03/19/2019 – 01/24/2020 |
| Food Universe | NY | Far Rockaway | 32-11 Beach Channel Drive | 03/13/2019 – 01/24/2020 |
| Food Universe | NY | Long Island City | 34-14 Steinway Street | 04/07/2019 – 01/24/2020 |
| Food Universe | NY | New York | 538 W 138th Street | 03/12/2019 – 01/24/2020 |
| Food Universe | NY | New York | 70-72 Nagle Avenue | 01/26/2017 – 02/25/2020 |
| Food Universe | NY | New York | 5069 Broadway | 01/26/2017 – 03/03/2020 |
| Food Universe | NY | Richmond Hill | 117-01 Liberty Avenue | 03/19/2019 – 01/24/2020 |
| Food Universe | NJ | Paterson | 498 East 30th Street | 04/08/2019 – 01/24/2020 |
| Gala Foods | NY | Brentwood | 725 Commack Road | 04/07/2019 – 11/01/2019 |
| Gala Foods | NY | Brentwood | 1925 Brentwood Road | 03/30/2019 – 01/24/2020 |
| Gala Foods | NY | Freeport | 111 W. Merrick Road | 03/30/2019 – 01/24/2020 |
| Gala Foods | CT | Bridgeport | 1050 East Main Street | 04/07/2019 – 01/24/2020 |
| Gala Foods | CT | Bridgeport | 1457 Fairfield Avenue | 04/07/2019 – 01/23/2020 |
| Gala Foods | MA | Worcester | 664 Main Street | 04/07/2019 – 01/24/2020 |
| GalaFresh Farms | NY | Bay Shore | 1819 Fifth Avenue | 03/28/2019 – 01/24/2020 |
| GalaFresh Farms | NY | Brooklyn | 492 St. Marks Place | 04/25/2017 – 01/26/2020 |
| GalaFresh Farms | NY | Riverhead | 795 Old Country Road | 04/08/2019 – 01/24/2020 |
| Gitto Farmer’s Market | NY | Brooklyn | 38 Brooklyn Terminal Market | 04/09/2019 – 02/14/2020 |
| Howard Avenue Market | NY | Brooklyn | 8 Howard Avenue | 01/12/2019 – 03/10/2020 |
| Jumbo Market | NY | Bronx | 1383 Nelson Avenue | 01/05/2019 – 02/14/2020 |
| Key Food | NY | Brooklyn | 6620 Avenue U | 03/06/2017 – 03/18/2020 |
| Key Food | NY | Brooklyn | 1610 Cortelyou Road | 03/19/2019 – 01/24/2020 |
| Key Food | NY | Jackson Heights | 86-02 Northern Boulevard | 03/13/2019 – 01/24/2020 |
| Key Food | NY | Jackson Heights | 3754 90th Street | 04/07/2019 – 01/24/2020 |
| Key Food | NY | Jamaica | 166-02 Baisley Boulevard | 05/29/2019 – 11/01/2019 |
| Key Food | NY | Rock Hill | 214 Rock Hill Drive | 04/07/2019 – 01/24/2020 |
| Key Food | NY | Spring Valley | 289 North Main Street | 03/19/2019 – 01/24/2020 |
| Key Food | NY | Valley Stream | 1805 N Central Avenue | 03/19/2019 – 01/24/2020 |
| Key Food | NY | Woodside | 61-10 Queens Boulevard | 01/26/2017 – 03/05/2020 |
| Key Food | CT | Waterbury | 286 Fairfield Avenue | 05/14/2019 – 01/24/2020 |
| Key Food | FL | Naples | 2668 Tamiami Trail E. | 04/30/2019 – 01/24/2020 |
| Latino’s Supermarket | NJ | West New York | 6418 Hudson Avenue | 01/27/2017 – 02/14/2020 |
| Marketplace | NY | Brooklyn | 617 Fifth Avenue | 03/08/2017 – 04/22/2020 |
| Neighbors Foodmarket | FL | Sunrise | 6041 W Sunrise Blvd. | 04/13/2019 – 01/24/2020 |
| Ozzie’s Fresh Market by Food Universe | NY | Brooklyn | 639 Grand Street | 04/06/2019 – 01/24/2020 |
| Price Choice Foodmarket | NY | Ridgewood | 64-01 Fresh Pond Road | 02/17/2017 – 02/14/2020 |
| The Food Emporium | NY | Brooklyn | 8102 3rd Avenue | 03/28/2019 – 11/01/2019 |
| Top Value Supermarket | FL | Miami | 1490 NW 3rd Avenue, Suite 101 | 04/08/2019 – 01/24/2020 |
| Tropical Supermarket | NJ | Dunellen | 446 North Avenue | 01/29/2017 – 03/17/2020 |
| Tropical Supermarket | NJ | North Brunswick | 959 Livingston Avenue | 01/26/2017 – 04/13/2020 |
| Tropical Supermarket | NJ | Perth Amboy | 442 Smith Street | 01/19/2017 – 02/14/2020 |
| Tropical Supermarket | NJ | Somerset | 720 Hamilton Street | 01/27/2017 – 03/17/2020 |
| Tropical Supermarket | NJ | South River | 62 Main Street | 01/26/2017 – 02/13/2020 |
| Tropical Supermarket | NJ | Union City | 2400 Central Avenue | 01/26/2017 – 04/17/2020 |
| Tropical Supermarket | NJ | Union City | 1208 New York Avenue | 01/27/2017 – 03/03/2020 |
| Vitelio’s Marketplace | NY | Kew Gardens | 116-15 Metropolitan Avenue | 01/23/2017 – 02/13/2020 |
| Waverly Gourmet Market | NY | Brooklyn | 367 Waverly Avenue | 04/09/2019 – 01/24/2020 |
| Location | State | City | Address | Exposure Time Period |
|---|---|---|---|---|
| Mega Package Store | GA | Suwanee | 2820 Lawrenceville-Suwanee Rd | 03/2020 – 06/2020 |
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.