
For decades, cybercriminals targeted the United States to the exclusion of most other countries. While the US remains the most targeted country, since 2015, when the US began adopting EMV technology, cybercriminals have scoured the world for new vulnerable targets. While the entire Asia Pacific (APAC) region is experiencing a noticeable uptick in attacks against brick-and-mortar and e-commerce businesses, South Korea has emerged as the largest victim of Card Present (CP) data theft by a wide margin. Although it initiated EMV chip adoption in May 2015 and mandated compliance by July 2018, CP fraud still frequently occurs. EMV chip adoption generally corresponds to far lower rates of CP fraud; however, the CP fraud rate in the United States remains high due to poor merchant implementation. This appears to be the case in South Korea as well.
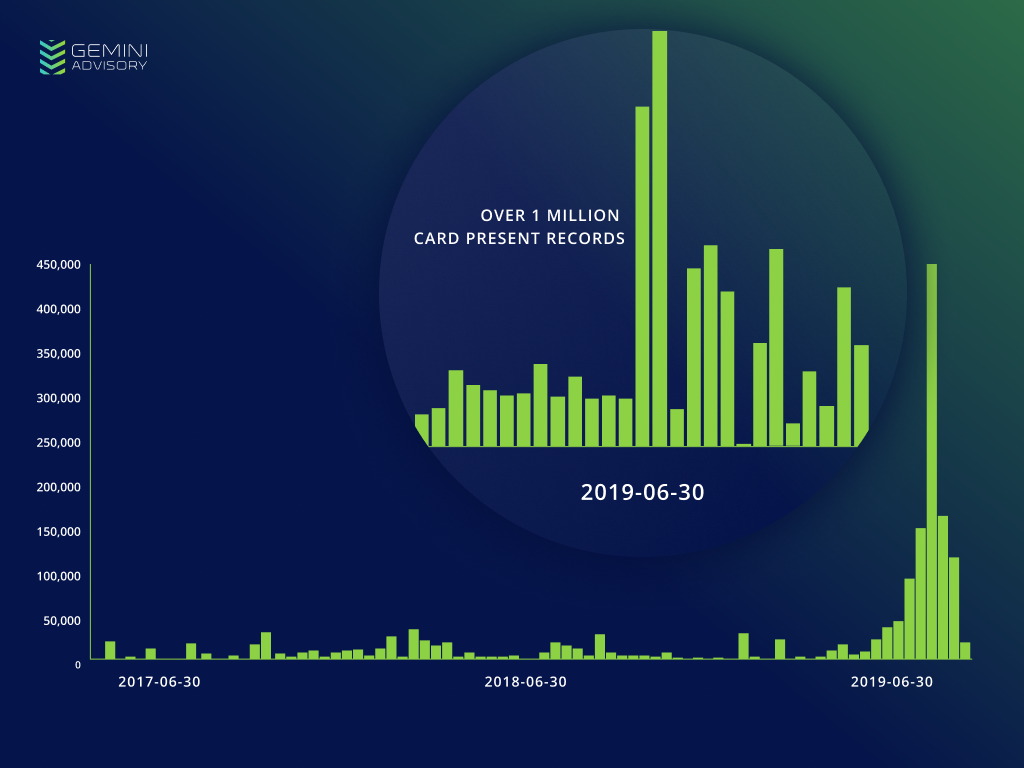
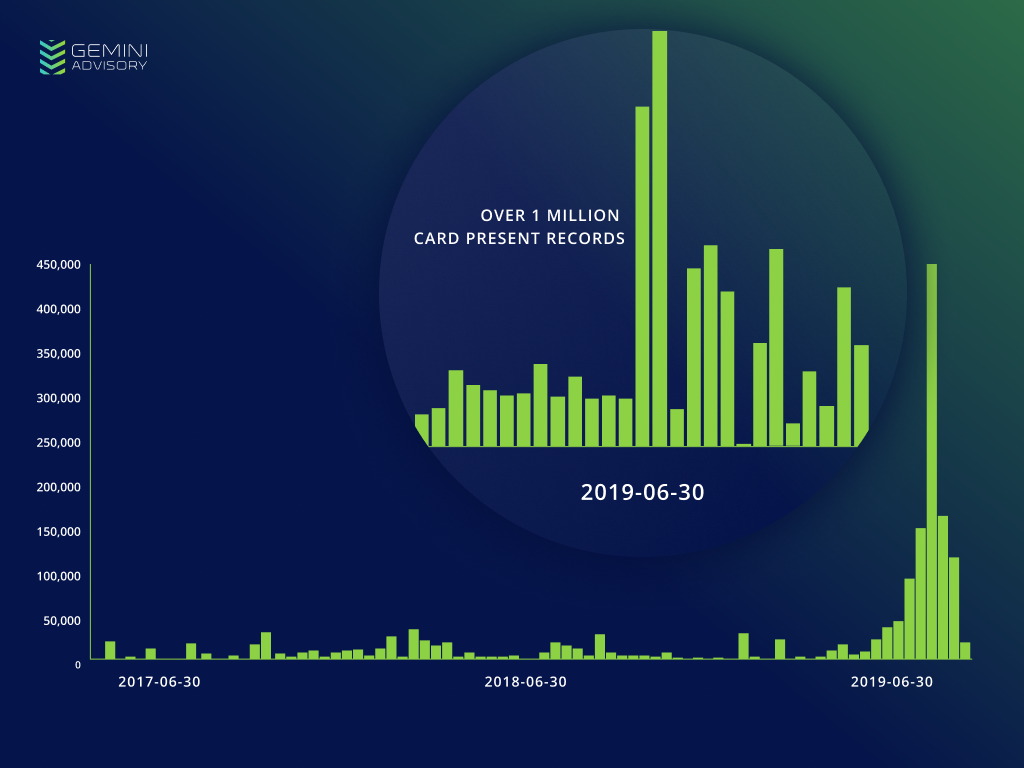
Gemini Advisory observed 42,000 compromised South Korean-issued CP records posted for sale in the dark web in May 2019, which is generally in line with monthly additions from the past two years. However, June 2019 had 230,000 records, a 448% spike. July was even more drastic with 890,000 records, a 2,019% increase from May’s benchmark amount. This spike currently consists of over 1 million compromised South Korea-issued CP records posted for sale in the dark web since May 29, 2019.
CP fraud involves collecting payment card information from in-person transactions. The most common way to do this is by installing malware into a system that has point-of-sale (POS) devices on its network. When a threat actor gains access to a system, they can install additional malware or backdoors in order to access card data. This POS malware can scrape random-access memory (RAM) to obtain card information from a device’s temporary memory before it is initially encrypted. The threat actor thus captures the desired plain text card data and can encrypt it and send it back to their own server.
Another method of obtaining CP record information involves using skimmers and overlays, devices that are installed at ATMs or POS terminals. These devices capture the information on a card’s magnetic stripe, allowing the fraudster to clone that card and make illicit payments of their own. However, EMV chips are prohibitively difficult to clone, so a fraudster would be unable to illicitly make a payment at a store that only accepts EMV chip payments and does not allow customers to swipe their cards.
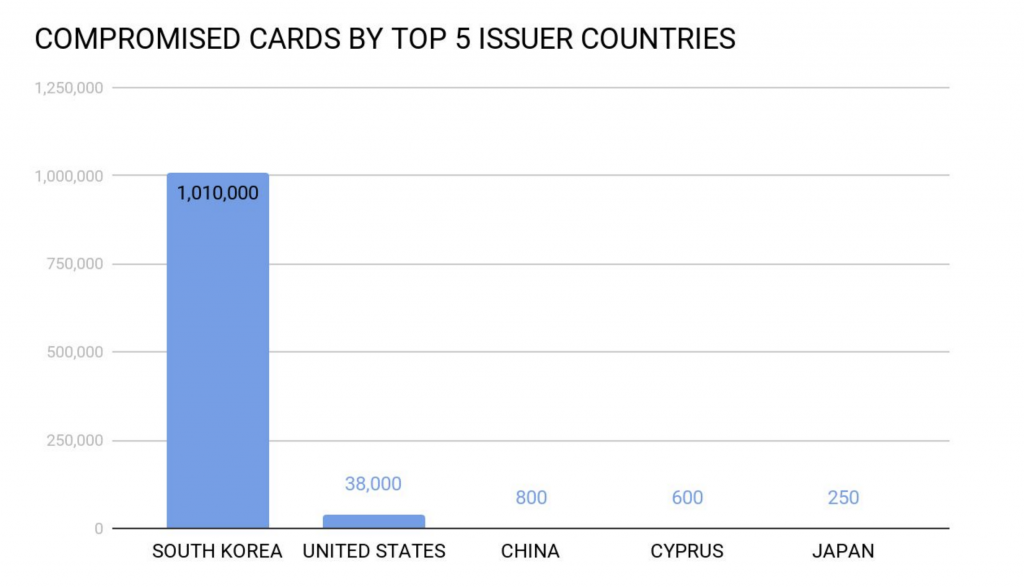
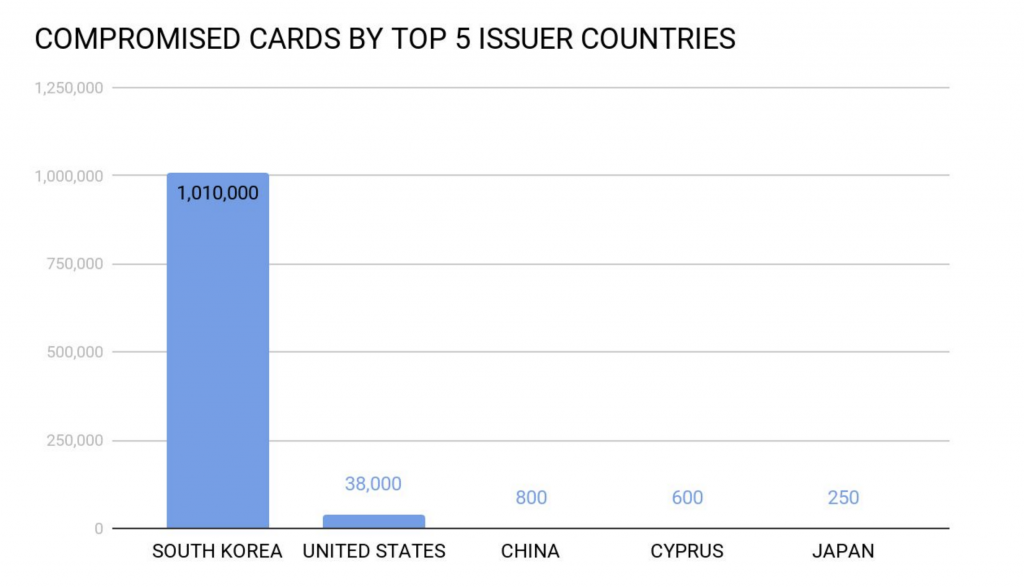
Among the additions of compromised South Korean CP records, Gemini identified that 3.7% were US-issued cards. One of the most affected US financial institutions was a credit union that primarily serves the US Air Force; the Air Force maintains multiple air bases in South Korea. Through an in-depth analysis of the compromised cards, analysts determined that many of them belong to US cardholders visiting South Korea. Since South Korea has received just over 1 million US travelers in the past 12 months, this should account for the high level of US payment records.
The median price per record from this spike is $40 USD, which is significantly higher than the median price of South Korean CP records across the dark web overall, which is approximately $24 USD. In 2018 there was a relatively large supply of South Korean records but a low demand. The following year saw a lower supply than 2018, but a growing demand. The demand continued to increase while the supply remained stagnant until the recent spike in South Korean records from June until the present. This sudden influx in card supply may be highly priced in an attempt to capitalize on the growing demand.
Gemini coordinated with several research teams to further explore potential compromised points of purchase (CPPs). However, these attempts were not fruitful since there were too many possible businesses affected by this breach. There are two likely scenarios that can explain this. The first is that the records were obtained from the breach of a parent company that operates several different businesses in a variety of locations. This would account for the large number of merchants and POS terminals affected by this breach. A similar incident occurred in the United States with the breach of Earl Enterprises, a parent company with six restaurant chains maintaining over 150 separate locations across the United States. The locations and POS terminals affected by the breach were spread across the United States, making it difficult to determine the CPP. This may be the same situation as in this South Korean breach.
It is also possible that a POS integrator was breached. This would mean that a threat actor gained access to a single integrator service that interfaces with many merchants to enable them to use their individual POS devices. The threat actor would then have access to payment data from multiple sources, accounting for the lack of a common merchant among the compromised payment cards.
Targeting integrators is now the top attack vector for payment card breaches, according to a Mastercard-issued report. Since successful integrators are often very busy, threat actors rely on leveraging shortcuts such as repeated passwords or single-factor authentication to gain entry. After gaining entry, often through phishing for remote access credentials, they can install malware on the connected merchant locations. Cybercriminals often operate at night and steal cards from only a few merchants at a time in order to lower the risk of detection.
As the Western world continues to invest in robust cybersecurity measures to secure payment transactions, cybercriminals have increasingly targeted new victims. Indian-issued payment cards have recently surpassed those of the United Kingdom to become the second-most targeted cards in the world in 2019. Even smaller economies, such as Pakistan, have seen massive breaches in recent years, such as 2019’s breach of Meezan Bank Ltd. South Korea’s high CP fraud rates indicate a weakness in the country’s payment security that fraudsters are motivated to exploit. As this global trend towards increasingly targeting non-Western countries continues, Gemini Advisory assesses with a moderate degree of confidence that both the supply and demand for South Korean-issued CP records in the dark web will likely increase.
Gemini Advisory provides actionable fraud intelligence to the largest financial organizations in an effort to mitigate ever-growing cyber risks. Our proprietary software utilizes asymmetrical solutions in order to help identify and isolate assets targeted by fraudsters and online criminals in real-time.